SOC 2 Type II for Healthtech Startups: The Ultimate Hospital Procurement Checklist

SOC 2 Type II has become a practical trust signal for healthtech startups. It shows your reliability as a partner during the hospital procurement process as a SOC 2 Type II report demonstrates effectiveness of your security controls over a prolonged period. This blog lists what the process entails and how you can build your own SOC 2 supported cybersecurity.
M&A Due Diligence: Why You Must Pentest an Acquired Clinic’s Web Apps Before Integration
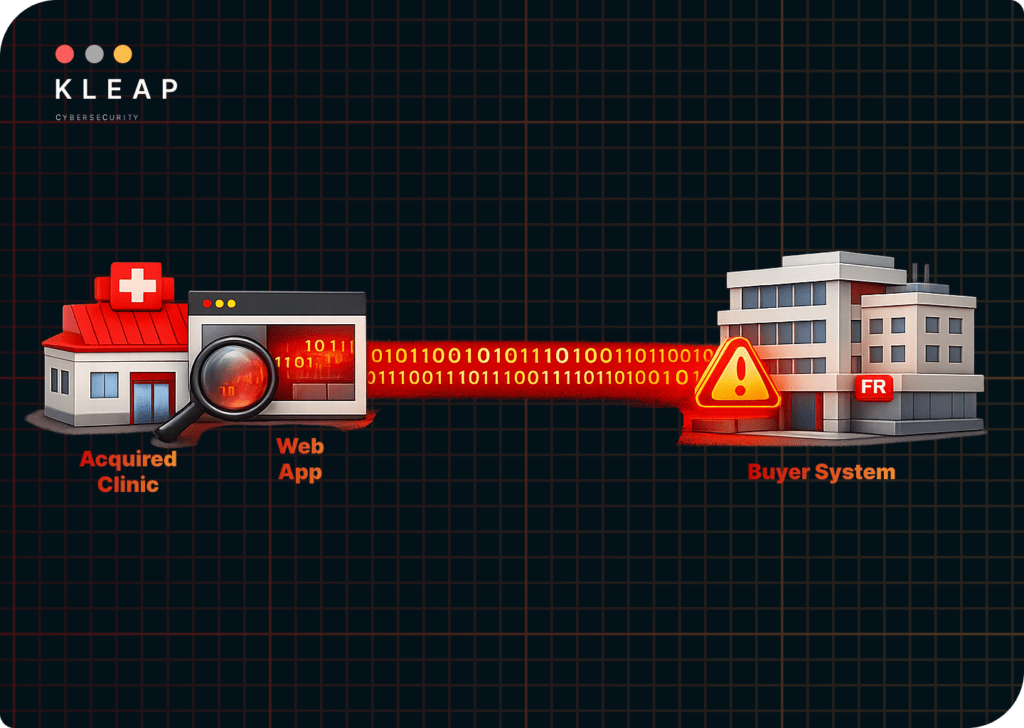
When a healthcare group acquires a clinic, web application security rarely makes the due diligence checklist. Every acquired clinic comes with a patient portal, billing apps, and EHR integrations carrying ePHI. Once the deal closes, their vulnerabilities are yours. Here are the risks that you inherit and what a pre-integration webtest should cover.
Securing ERP API Integrations: Prevent Vendor Apps from Exposing Supply Chain Data

API integrations in ERP are a bigger risk than anyone can anticipate. ERPs handle sensitive information about clients, finance, and machine specifications. A compromised vendor and underlying API vulnerabilities can wreak havoc. Manufacturing data breaches not only affect your production, but also the entire supply chain you cater to.
Active Directory Pentesting

For most organizations, a single compromised account is all it takes to have a major incident and credibility loss – and most teams don’t realize how short that path really could be in their environment. This case study walks through a real KLEAP Active Directory pentesting engagement – the client’s objective, the attack paths we identified, […]
AI & HIPAA Violations: From Real-World Impact to Mitigating Security Risks

In the AI-era, negligence of organizations and ignorance of care providers are giving rise to new security risks. This blog investigates real-world reports, and charts a course through the deployment process, giving a step-by-step guide to meet HIPAA compliance.
HIPAA Compliance & Security for Federally Qualified Health Centers
Unlike other healthcare providers, Federally Qualified Health Centers operate on a fixed budget with severe staff shortage. Oversights, poor technical safeguards, and lack of personnel training make PHIs the most vulnerable target in an FQHC ecosystem. FQHCs need specialized safeguards and a system that makes them ready for HIPAA compliance.
Automated vs. Manual Web App Pentesting: A Cost-to-Risk Guide for IT Directors
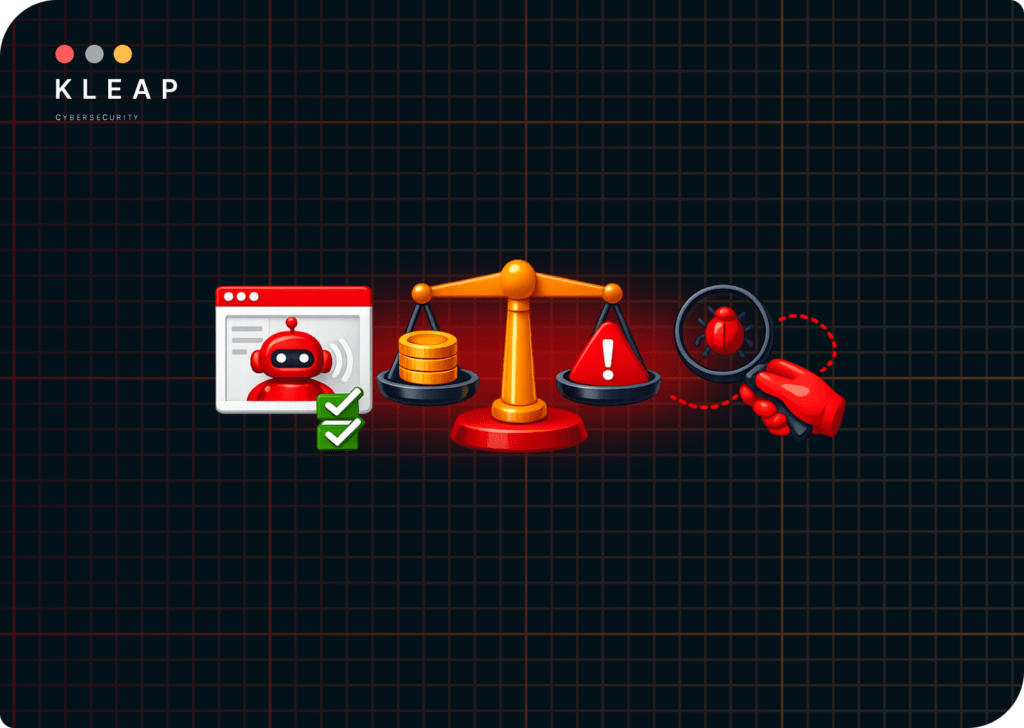
Automated and manual web app pentesting aren’t two versions of the same thing at different price points. They test for fundamentally different categories of risk. This guide breaks down what each approach covers, where the pricing comes from and the specific aspects that only manual testing catches and automated tools miss out.
Securing CUI in the Cloud: CMMC Readiness for Manufacturing Web Portals

Manufacturing web portals weren’t built as compliance boundaries. Under CMMC 2.0, if your supplier portal or technical data exchange handles controlled unclassified information, it’s in scope, and a FedRAMP-authorized cloud doesn’t automatically make it compliant. Here’s what CMMC readiness actually requires for cloud-hosted manufacturing portals before a C3PAO shows up.
Business Associate Agreement: A Complete Guide for Healthcare Orgs

A BAA is a legal instrument; it assigns responsibility and creates liability, but it does not verify that a single security control has been implemented. This guide examines where BAAs fail in practice, what OCR enforcement actions reveal, and what IT teams need to do differently to make their vendor relationships genuinely defensible.
Prove IT/OT Segmentation in Manufacturing with Internal Network Pentesting

Manufacturing networks carry two high-value targets in the same building: the corporate IT environment and the OT systems running production. This blog explains what internal network pentesting actually tests, why assumed segmentation consistently fails, and how to produce verified proof that your IP is protected.