Healthtech companies usually face intense scrutiny from enterprise hospitals than from regional clinics.
The reason is simple: They want to make sure your security posture has the right controls in place to safeguard their confidential data.
Suddenly, you go from answering questions about your product to answering vendor risk questionnaires that ask whether your company is safe enough to trust inside a hospital environment.
The vendors who close deals are the ones who are already prepared, as their checklist also another element: a SOC 2 Type II report.
System and Organization Control 2 is an auditing framework developed by the American Institute of Certified Public Accountants (AICPA) that evaluates whether a technology company’s controls for protecting customer data meet a defined set of standards.
It is not a replacement for HIPAA or a shortcut around a BAA. It simply tells the hospital buyer that your controls were not just drafted but tested over time.
For healthtech companies, the relevant criteria are almost always Security, Confidentiality, and Privacy as these align most directly with HIPAA’s requirements for protecting ePHI.
However, unlike HIPAA, the SOC 2 compliance requirement for healthcare technology is not a legal mandate. But it raises trust with the procurement team, which benefits you in closing the deal sooner.
That said, the benefits don’t end there.
How SOC 2 Fits into Your Security Plan
SOC 2 for healthcare is most effective when it functions as the organizing framework for a startup’s entire security program from the very beginning. It should be seen as more than just compliance.
The benefits of pursuing SOC 2 Type II early are plain to see:
- It accelerates the hospital procurement process by reducing extensive security reviews.
- It surfaces security gaps before they are discovered during a vendor management process, or worse, during a data breach afterwards.
- It provides a structured evidence report for HIPAA risk analysis under 45 CFR 164.308(a)(1), since many SOC 2 controls map directly to HIPAA Security Rule safeguards.
- It builds investor confidence. PwC’s 2022 Global Investor Survey states about 51% of investors believe companies should prioritize investments in cybersecurity and data privacy to build trust. By now, this number is expected to be higher.
- It supports faster contract execution. Vendors with current SOC 2 Type II reports will have an easier time with the vendor risk questionnaire review.
While SOC 2 has its benefits, it is important to know one report type can give you an edge over the other. Most healthcare startups have a limited budget and opt for the Type I report. Others have no idea about the distinction.
Let’s dive deeper into it.
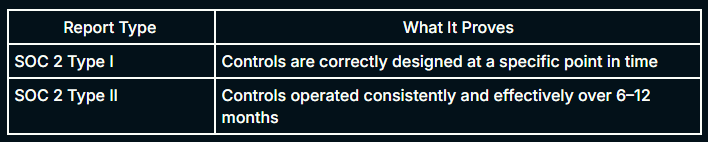
SOC 2 Type II vs. Type I: The Distinction That Kills Deals
Hospital procurement teams may not feel confident looking at your SOC 2 Type I report.
Type I is a point-in-time assessment. It tells a procurement team that your controls were designed correctly on the day the auditor reviewed them.
It says nothing about whether those controls are operating consistently over time.
In contrast, SOC 2 Type II demonstrates whether the controls can operate effectively over an observation period of six to twelve months.
Even in the case of HIPAA compliance, large hospital networks look for Type II reports because it tests whether the controls actually operated consistently over months. And one missed control test constitutes an exception in the auditor’s opinion.
There are some additional scope issues that matter to the hospital procurement process specifically:
- Audit period length: A 12-month observation period is the preferred standard for procurement teams. Shorter periods raise questions about whether the vendor was getting organized for the audit rather than operating consistently.
- Scope Exclusions: If the SOC 2 Type II report does not cover the systems procurement cares about most such as the patient-facing application, the API handling PHI, and the data pipeline, then the scoping gap will be noticed.
For startups in early hospital conversations with only a Type I report, the path forward is to be transparent about the Type II timeline and not present Type I as equivalent. Procurement teams who discover a misrepresentation mid-review will not feel the vendor as trustworthy.
The SOC 2 Type II Journey: Scoping, Implementation, and Audit Preparation
Understanding the SOC 2 compliance requirement is one thing, but building the program is another ballgame. Every phase of the SOC 2 Type II journey maps directly to aspects that the hospital procurement teams will examine.
The timeline from scoping to a completed Type II report runs approximately 10-12 months. Let’s break down the timeline according to phases and see what function each of them delivers.
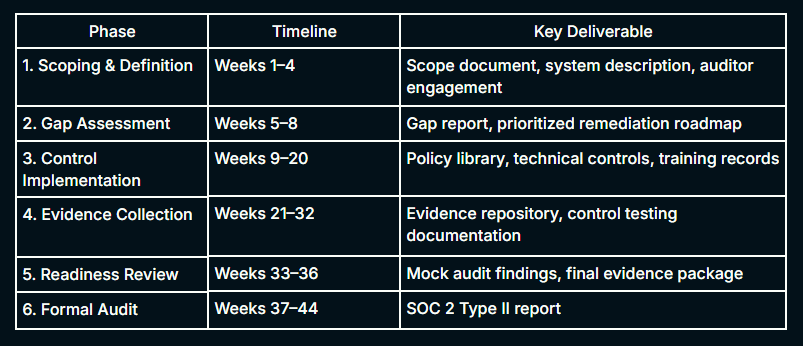
Phase 1: Define Your Scoping Before You Build
Scoping impacts everything in SOC 2 for healthcare startups. If you get it wrong, you either leave systems critical to the procurement audit outside the audit boundary, or you scope too broadly, driving up audit cost and complexity without meaningful benefit.
Healthtech startups should always include the Security Trust Services Criterion and add Confidentiality and Privacy if they are handing PHIs. Some of the key scope decisions they should take are:
- Systems in Scope: Identify every system that stores, processes, or transmits ePHI. This includes your applications, APIs, databases, cloud infrastructure (AWS, Azure, etc.), data pipelines, and any third-party integrations with PHI access. It is also recommended to evaluate your EHR data storage.
- Trust Services Criteria Selection: For hospital procurement, Security is mandatory. Confidentiality and Privacy are expected given PHI handling. Availability is relevant if you’re signing an uptime SLA.
- Audit Period Definition: The observation period should run for at least 12 months. Procurement teams become wary when the report is more recent than that.
- Auditor Selection: Choose an AICPA-registered CPA firm with demonstrated healthtech experience. The auditor must be reputed and understand how healthcare applications handle PHI and what HIPAA risk analysis requires in terms of the evidence.
Phase 2: Gap Assessment to Know What You Are Missing
Before any control is built, a gap assessment establishes the distance between your current security posture and what SOC 2 Type II requires.
A thorough assessment of current controls across all five Trust Services Criteria areas should be done with explicit identification of gaps and a remediation roadmap to close them.
For healthtech startups, gap assessments commonly surface four recurring findings:
- Missing or undocumented policies: When technical controls exist but have no written policy behind them. Auditors require both.
- Incomplete audit logging: This happens when the IT infrastructure logs exist, but PHI access logs are absent or incomplete.
- Access control gaps: Gaps in access appear when RBAC is not consistently enforced or the offboarding process are not documented properly.
- Third-party risk blind spots: When subprocessors touching PHI are not documented in the security reviews.
The gap assessment should come with a remediation roadmap, not just a list. Critical gaps affecting PHI confidentiality and integrity should be addressed before the observation period begins.
Phase 3: Control Implementation
Control implementation is not just writing policies. It is operationalizing controls so that they run consistently, generate evidence automatically where possible, and can be demonstrated under auditor examination.
The AICPA’s Security Trust Services Criterion is structured around nine Control Components from CC1 to CC9. They cover the control environment, risk assessment, monitoring activities, logical and physical access, system operations, change management, and risk mitigation.
In healthcare, control implementation must also account for HIPAA-specific requirements that sit alongside SOC 2:
- HIPAA Administrative Safeguards (45 CFR 164.308): These are HIPAA’s administrative safeguards that cover security management processes, workforce training, contingency planning, and evaluation.
These map to SOC 2’s risk assessment and monitoring control components.
- HIPAA Technical Safeguards (45 CFR 164.312): These include access controls, audit controls, integrity controls, and transmission security.
They map directly to SOC 2’s access control and encryption requirements.
- HIPAA Physical Safeguards (45 CFR 164.310): These take into account the access controls and workstation security. These are typically covered by cloud provider controls for cloud-native startups, but the startup must document that coverage explicitly.
Documentation is a must at this stage. Controls without documentation do not count in a SOC 2 audit. Every implemented control needs a written policy that describes the requirement, the frequency of execution, and how evidence is captured.
Phase 4: Evidence Collection
SOC 2 Type II is all about evidence collection. The auditor’s job is to test whether controls are operated as documented throughout the observation period of 12 months.
The startup’s job is to document that evidence continuously and not to scramble in the final weeks before the audit.
Evidence categories that auditors sample during a SOC 2 Type II audit for healthcare include:
- Access review records: These are quarterly user access records that prove manager approval of current access levels.
- Audit logs: These are application-level records of PHI access events, showing who accessed what data, when, and through which endpoint.
- Vulnerability scan results: There should be a semi-annual vuln scan that comes with proper remediation tracking.
- Security awareness training records: Records showing completion of training for all staff with PHI access.
- Change management records: A structured record of transfer of individuals or teams through approval trails and change logs.
- Incident response documentation: These are records of any security incidents during the observation period, how they were handled, and the timeline from detection to resolution.
- Vendor review records: This includes evidence of security reviews conducted for subprocessors with PHI access.
Phase 5 & 6: Readiness Review and Formal Audit
A readiness review is an internal mock audit conducted before the formal engagement. It tests a sample of evidence and identifies any last-minute gaps before the auditor arrives.
For healthtech startups, the readiness review should also include a call preparation session for the technical staff who will be questioned by the auditor directly.
The formal audit fieldwork typically runs for two to four weeks, with an additional two to four weeks to submit the final report. After the auditors have reported their findings, you have the opportunity to review and respond to them.
This is also where you can explain the excluded scope. A report with unresolved exceptions is not procurement-ready.
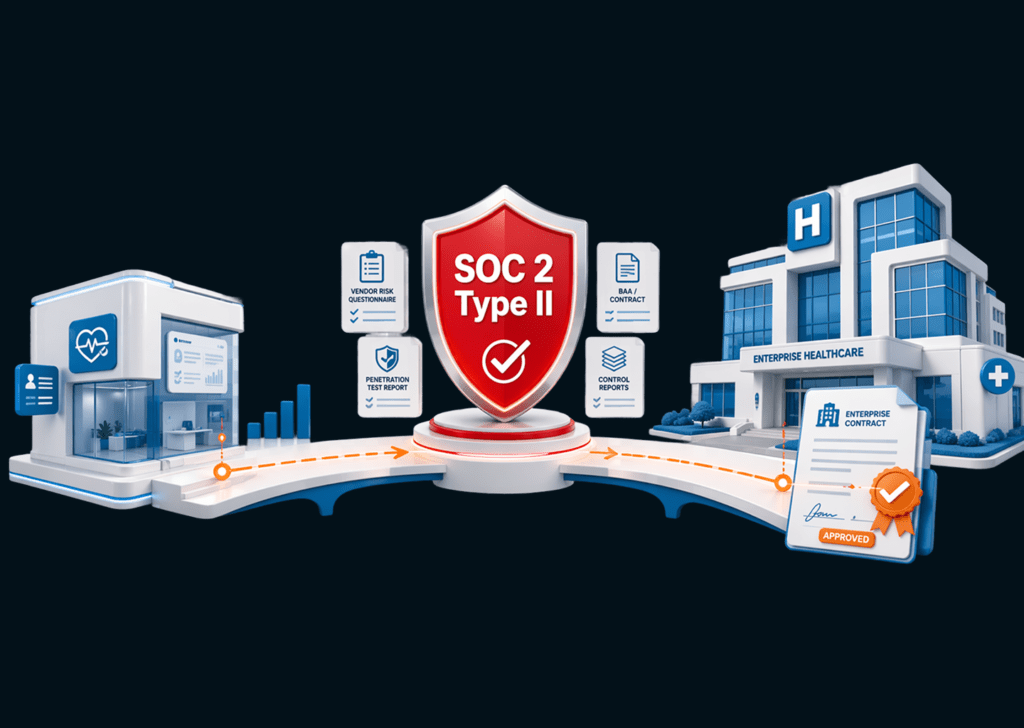
Building Your Procurement-Ready Security Package
Vendors who quickly navigate the hospital procurement process are usually the ones who are equipped with a comprehensive security package from the start.
This readiness doesn’t stem from anticipating every question but from having a solid foundation in security.
Data breaches due to third-party involvement had doubled to 30% in 2025 according to Verizon’s Data Breach Investigations Report.
SOC 2 compliance is thus becoming essential for enterprises, and, for healthtech startups targeting hospitals, the standard is even higher.
Here’s what your program should demonstrate across the eight control areas procurement will investigate:
-
Risk Assessment and Management: Hospital procurement consistently checks for a formal process in place for identifying and managing risks rather than a reactive approach. This involves having a documented risk policy, a detailed risk register, and regular reviews, which specifically addresses ePHI threats.
In SOC 2 for healthcare, the risk register must account for PHI-specific threat as well.
-
Access Controls and Identity Management: You have to enforce robust authentication and RBAC since procurement will examine controls like single sign-on, mandatory multi-factor authentication, role-based access control, and documented offboarding processes.
You need to have your role definitions, access review records, and offboarding checklist ready.
-
Data Encryption: Encryption addresses the Confidentiality Trust Services Criterion in SOC 2 for healthcare. All data, especially ePHIs, should be encrypted at rest and in transit with encryption in all storage containing customer data.
You have to be prepared for questions like what cipher standards are in use, who controls the encryption keys, and what happens to encrypted data when a contract terminates.
-
System Monitoring and Audit Logging: This is both a SOC 2 and HIPAA requirement. For monitoring to happen, you need to centralize all your logs, which includes application logs, authentication logs, and even network firewall logs.
The common gap hospital procurement finds most often is application-level PHI access logs. That absence is a HIPAA audit control failure, not just a SOC 2 gap.
-
Vulnerability Management and Penetration Testing: A vulnerability management policy should be in place that defines the frequency of testing. Not only are the scan reports crucial, but also documentation of the same.
Annual penetration testing must also be scoped to the system. The 2025 HIPAA Security Rule has already made it an explicit requirement.
-
Incident Response: Your incident response plan must be documented and tested. For SOC 2 for healthcare, it should also meet HIPAA’s breach notification requirements.
Under 45 CFR 164.400–414, business associates must notify the covered entity of a breach without unreasonable delay and no later than 60 days after discovery. The Incident log should also show any security events during the SOC 2 observation period and their resolutions.
-
Vendor and Sub-processor Management: Hospital procurement will request your full sub-processor list and compare it against your BAA’s sub-processor coverage. Any tool that touches PHI and is not listed will be flagged down.
Maintaining compliance requires a current inventory of every third-party tool with PHI access, the category of data they receive, the legal agreement governing that relationship, and the security certifications those vendors hold.
-
Change Management and Secure Development: Hospital procurement teams will ask how code changes are reviewed before reaching production and whether security testing is part of the development lifecycle.
You need to be ready with evidence of code review processes and the change management policy with defined approval requirements.
How KLEAP can help
KLEAP conducts manual web application, API, and network penetration tests scoped to the specific systems healthtech startups expose to hospital procurement review.
Every engagement is led by a dedicated security expert who understands how healthcare applications handle PHI and what HIPAA’s risk analysis requirements demand in terms of documented evidence.
Kleap’s concierge model ensures that you get a dedicated expert who scopes your organizational needs, manually conducts risk assessment, and explains every finding to your compliance officer or your board.
Our experts nderstands how healthcare applications handle PHI and what HIPAA’s risk analysis requirements demand in terms of documented evidence.
For healthtech startups building toward a SOC 2 Type II report and preparing for the hospital procurement process, KLEAP not only provides support for framework compliance but also provides hands-on vulnerability assessment and penetration testing scoped to your actual environments.
This includes patient-facing APIs, authentication flows, and third-party integrations. We deliver findings mapped to HIPAA Security Rule controls and provide a remediation roadmap that gives your team a clear path from assessment to procurement-readiness.
If you are aiming for an enterprise hospital contract and are not certain your security posture will survive a rigorous vendor review, KLEAP can provide a detailed scope assessment in one call.