HIPAA compliance for Ambulatory Surgery Centers can’t stay a once-a-year paperwork exercise. Learn what real HIPAA readiness looks like for ASCs: a living risk analysis tied to remediation ownership, continuous monitoring and validation of safeguards, and stricter vendor governance that helps ASCs stay continuously audit-ready while protecting operational continuity.
About 6,300 ambulatory surgery centers (ACSs) treated 3.4 million fee-for-service Medicare beneficiaries.
That was three years ago.
Industry forecasts project the U.S. ASC market size to be in the $75 billion range by 2030, which isn’t surprising because they deliver routine procedures at a lower cost than hospital outpatient departments (HOPDs).
But this rapid growth is changing the sector’s risk profile.
ASCs run on a stitched-together tech stack with different tools and multiple vendor tools that access the same patient record at different points in the care journey.
More cases mean more Protected Health Information (PHI/ePHI), more systems, more vendor touchpoints, an expanding attack surface, and more compliance pressure.
Case in point, the Syracuse ASC settlement. Last year, they were penalized $250,000 because OCR found two concrete compliance failures after investigations into a 2021 ransomware incident.
- They had not conducted a thorough HIPAA Security Rule risk analysis of the risks and vulnerabilities to the ePHI in its environment.
- They failed to provide timely breach notifications as required under the HIPAA Breach Notification Rule.
The ruling also requires them to submit a two-year corrective action plan that specifically mandates completing a compliant risk analysis and implementing a risk management plan, alongside updated policies and workforce training.
The takeaway for ASC healthcare compliance is clear: HIPAA risk analysis and evidence-backed execution are the compliance foundations auditors expect to see.
HIPAA-Compliant Healthcare Challenges Ambulatory Surgery Centers Run Into
ASC healthcare compliance breaks because the compliance audit is often viewed as a documentation project while regulators test operational reality. HIPAA compliance requires an accurate and thorough risk analysis that includes ePHI handled across your systems and vendors.
It should also be noted that being compliant ≠ being secure, but more on that later.
ASC systems optimize for speed and volume, which is also why access control gets messy: staff inherit broad permissions, temporary users linger, and “just give them access” becomes the default response to avoid inconveniences.
Then there’s ePHI, which moves through scheduling, EHR workflows, billing, portals, telehealth, secure messaging, and vendor support tools; ergo, every ePHI handoff creates compliance and security risks.
When these tools don’t integrate cleanly, staff compensate around the system: exports, local saves, manual uploads, screenshots, email threads, spreadsheets, etc. That creates uncontrolled copies of PHI, slows evidence retrieval, and creates undocumented workarounds.
And finally, your risk analysis drifts every time ASC workflows change, unless it’s tied to a backlog and a cadence. Teams can’t clearly answer where ePHI flows, who touches it, and what safeguards apply at each handoff. This is how risks and vulnerabilities start spreading.
The Cybersecurity Controls ASCs Require for HIPAA Compliance
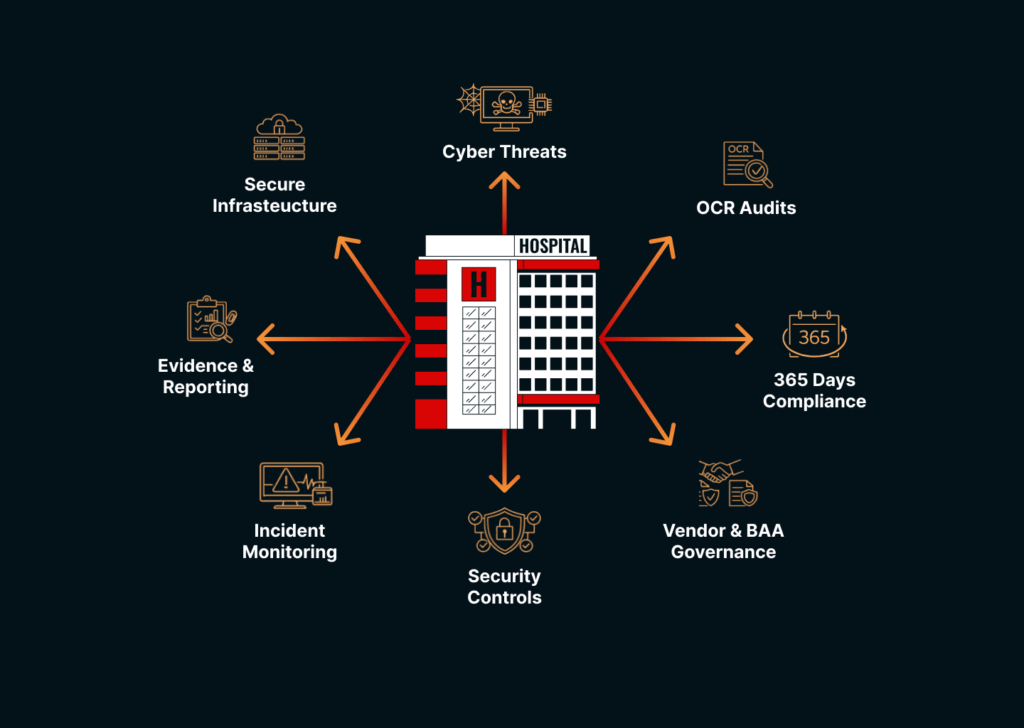
HIPAA doesn’t prescribe a single tool stack. But it does expect safeguards that are grounded in a thorough and demonstrably verifiable risk analysis. Which means to stay audit-ready, your HIPAA-compliant healthcare risk analysis must cover PHI you create, receive, maintain, or transmit, including ePHI handled by vendors and third parties.
Encryption You Can Prove
Ransomware and data exposure scenarios don’t care what your policy is; all that matters is what’s protected. Auditors focus on
- ePHI in transit (between systems, portals, telehealth, and vendor links).
- ePHI at rest (servers, cloud storage, backups, endpoints).
- ePHI management, access, and distribution documentation.
Evidence: configuration exports, encryption posture reports, and device encryption enforcement proof.
Audit-Ready Documentation
OCR audits are increasingly focusing on Security Rule provisions relevant to hacking and ransomware, which increases the importance of operational logging proof.
- Centralized logging for critical systems (EHR, portals, billing, identity).
- Log retention aligned to your risk and operational needs.
- Routine review cadence with documented follow-ups.
Evidence: SIEM/log dashboard screenshots alone aren’t enough; keep review records and exception handling notes.
Correctly Configured Integrations & PHI Handoff Controls
HIPAA risk analysis explicitly expects you to consider ePHI you create/receive/maintain/transmit, including flows involving vendors/consultants.
- Secure integration patterns between interoperating systems.
- Controls that prevent spreadsheet/email workarounds.
- Data minimization: only share what’s required.
Evidence: integration diagrams, data flow maps, access logs for integration service accounts, and change control records
Backups + Recovery that Address Real Cyber Threats
HIPAA’s ransomware guidance reinforces preparedness and recovery expectations as part of protecting ePHI and maintaining compliance.
- Backups that are air-gapped/protected.
- Recovery tests on a scheduled basis.
- Clear RTO/RPO expectations for critical workflows.
Evidence: recovery test results, restore logs, and documented recovery runbooks.
Provable Vendor & Third-Party Controls
BAAs are mandatory, but they need a system of enforcement that flags exceptions.
- Full inventory of vendors that touch ePHI.
- Signed BAAs + renewal tracking.
- Vendor access control (time-bound, privilege hierarchy, monitored).
- Security assurance collection (incident process, controls, contacts).
Evidence: vendor register, access logs, vendor review notes, and termination/offboarding proof.
Incident Readiness with Artifacts
HIPAA breach response expectations and timelines are operational, and you need to show proof that you can execute when something breaks.
- Incident response roles and escalation paths.
- Tabletop or walkthrough notes.
- Breach scoping workflow.
- Communications plan aligned to breach notification timelines.
Evidence: incident tickets, scoping templates, and post-incident action tracking.
Building a Sustainable Workflow for ASC Healthcare Compliance
One simply cannot treat ACS healthcare compliance as an annual event.
ASCs already operate under evidence-based oversight. The Centers for Medicare & Medicaid Services (CMS) surveys don’t just check documents; they look at how care is delivered in practice and cite gaps based on what audits check for.
HIPAA compliance for ASCs is moving the same way. OCR audits are increasingly focusing on the HIPAA Security Rule dealing with hacking and ransomware, which means teams must prove safeguards work.
- Map your PHI boundary once, then keep it current.
- Convert risk analysis into a remediation backlog with defined owners.
- Build an evidence documentation system that has a validation cadence.
- Treat vendor governance as a workflow.
- Make breach readiness a practiced process.
This gives you the ability to
- respond to an OCR request without a scramble.
- show evidence controls fast.
- keep ASC healthcare compliance current as tools and vendors change.
- reduce both compliance risk and operational disruption.
Why Trust KLEAP for HIPAA Compliance Services
HIPAA compliance services for ASCs must now focus on continuous validation of evidence and third-party governance, not just proper documentation.
ASCs need a compliance guide who runs the work like a concierge and makes HIPAA readiness predictable with zero ambiguity. KLEAP ensures you always know:
- What’s the scope
- Why it needs to be done
- Where proof exists
- How we’re getting you audit-ready fast
So, ASC healthcare compliance stays defensible even when tools, vendors, workflows, and standards change. If you’re looking for a reliable healthcare compliance partner: