Today, most medical devices are connected to the hospital’s network. From patient monitors to imaging devices, they transmit patient data in real time through Bluetooth, Wi-Fi, and cellular networks.
And, if you’re a Texas healthcare facility running these devices daily, you now have to comply with medical device security more strictly.
The latest directive from the Texas Health and Human Services Commission (HHSC) requires all healthcare facilities in the state of Texas to align with FDA cybersecurity guidance in matters of device procurement, maintenance, and decommissioning.
It comes after Governor Greg Abbott on March 9, 2026, issued a formal letter directing state health agencies to immediately review the cybersecurity posture of their networked medical equipment.
Most IT teams in healthcare have spent years focused on EHRs, cloud apps, and endpoint security. Connected medical devices have largely been treated as clinical infrastructure outside the IT security perimeter.
That changes now with the new medical security directive.
To give you a better understanding of what the directive specifically requires and what compliance challenges Texan hospitals will face, this blog gives you a complete rundown and tells you what your security program needs to meet compliance.
What Triggered the Texas Directive
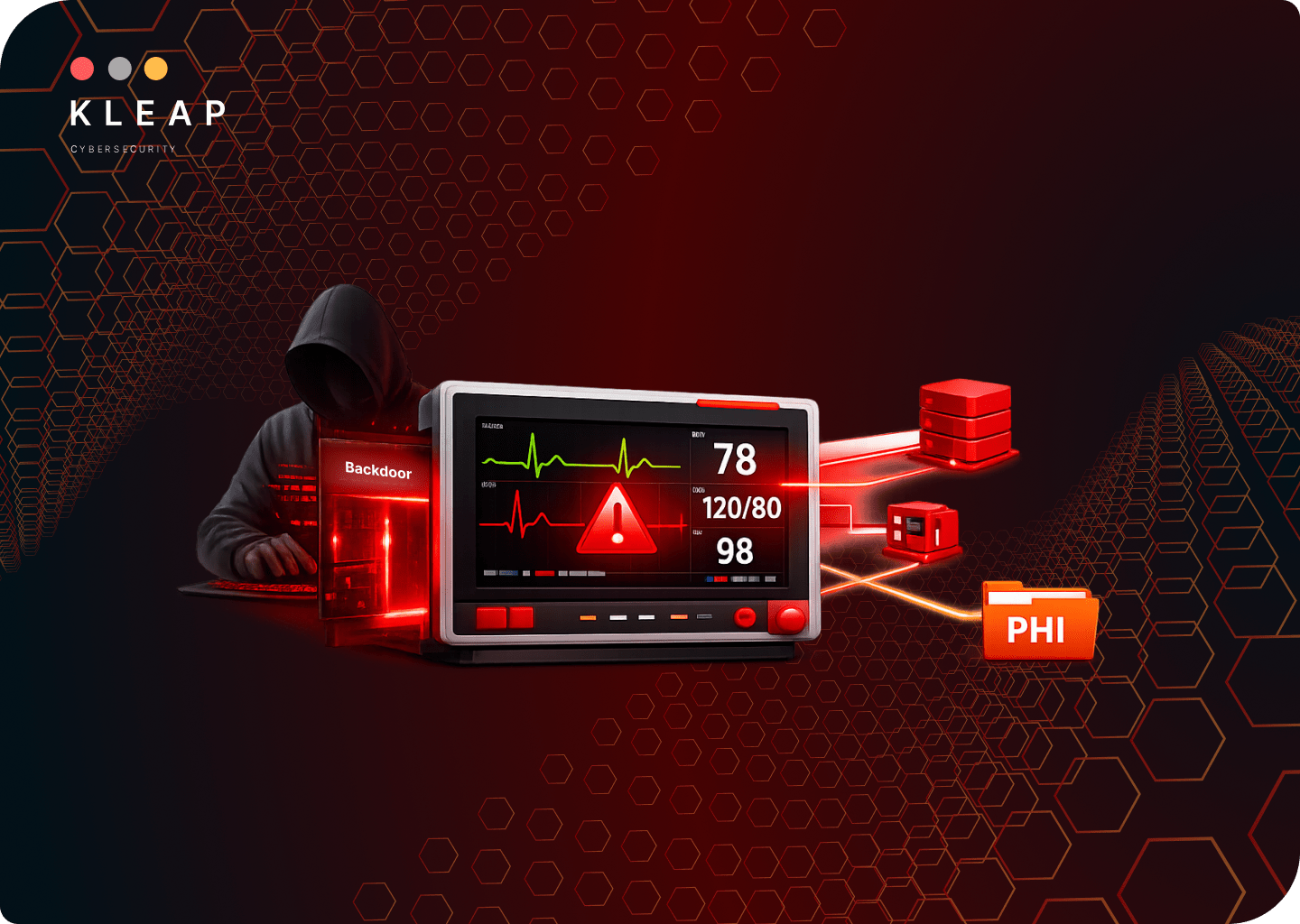
The governor’s directive cited alerts from both the Cybersecurity and Infrastructure Security Agency (CISA) and the FDA warning that the Contec CMS8000 and Epsimed MN-120 patient monitors contain serious vulnerabilities.
The reason was a hidden backdoor in these monitors that can allow unauthorized actors to remotely access the devices or the networks to which they are connected.
Regulators also found that these monitors may collect patient data including PHIs and transmit it outside the healthcare environment when connected to the internet.
The FDA was the first to issue a warning on these devices on January 30, 2025. However, it was CISA that found that the Contec CMS8000 contains a backdoor in its firmware that connects to a Chinese IP address and transmits patient data without notifying the hospital or the patient.
While CISA’s official recommendation was a blanket ban on CMS8000, the FDA recommended health facilities to email Contec for a software patch to remove the network function entirely.
In response, Governor Abbott released a letter directing the HHSC to take action. The HHSC expanded on that and formally brought all healthcare facilities in Texas, not just state-owned ones, under the directive to align with FDA cybersecurity guidance for medical devices.
What FDA Cybersecurity Guidance Is HHSC Asking Medical Facilities to Follow
The U.S. Food and Drug Administration (FDA) is intensifying its focus on cybersecurity in medical devices, having updated its guidance in 2025 and now in 2026.
The new Compliance Program Manual (#7382.850) which went effective from February 2, 2026, includes cybersecurity protocols to assist investigators with compliance during inspections.
The FDA’s cybersecurity guidance for medical devices distinguishes between pre-market requirements and post-market requirements. The pre-market requirements apply to manufacturers, while post-market requirements, apply to healthcare organizations operating medical devices.
The HHSC wants Texas healthcare providers to use the same guidance to review their medical devices and mitigate the risk of PHI breach.
The directive lays out four expectations:
- Review applicable FDA cybersecurity guidance for every medical device in use within their organization.
- Align procurement, maintenance, and decommissioning policies with that guidance.
- Assess every device with network functionality or remote access capability for potential cybersecurity risk.
- Coordinate with device manufacturers, vendors, and internal IT and security teams to identify and mitigate vulnerabilities.
For your Texas-based healthcare clinic, medical device security is now an explicit healthcare compliance obligation. It is now enforceable under both state directive and federal guidance.
Healthcare compliance in Texas now requires security programs that extend to every device capable of transmitting patient data.
The Challenges the HHSC Directive Creates for Texas Hospitals

On top of HIPAA compliance, you will now have to make structural changes to make room for FDA’s own updated guidance, which can prove difficult.
The core challenge is that hospitals must now map their entire device ecosystems to determine which devices qualify as “cyber devices” under federal criteria. Section 524B of the guidance states that these are devices equipped with software, including firmware or programmable logic, that connects to the internet.
This means any device equipped with Wi-Fi, cellular, Bluetooth, RF communications, or hardware connectors such as USB or Ethernet falls under this category.
Older devices, not originally designed for internet connectivity, can still have features like USB ports. In most Texas hospital environments, cataloguing, assessing their vulnerabilities, and applying fixes becomes a resource problem.
1. No single team has authority over the devices.
Medical devices live at the intersection of clinical engineering, IT, and security. In most facilities, none of those teams have full visibility or authority over the devices.
The directive requires a coordinated response that your organization might not have.
2. Device inventories are incomplete.
Clinical engineering records track biomedical assets for maintenance, not cybersecurity. They do not capture your firmware versions, network connectivity behavior, or data transmission destinations.
Meanwhile, IT asset management tools track endpoints that are enrolled in management systems, which most medical devices are not. Building a security-grade inventory from scratch under a deadline of the directive is a significant undertaking.
3. Many devices cannot be patched.
Most medical devices in Texas hospitals include equipment that runs end-of-life firmware, operating systems with no vendor support, and proprietary software that cannot be modified without voiding manufacturer agreements.
For these devices, the compliance path includes segmentation, access restriction, and monitoring.
4. Old devices may not meet compliance.
Executive Order GA-48 restricts the procurement of certain foreign-manufactured technologies for state facilities. But there are some devices that were already in place before this framework.
Confirming compliance for existing devices will require you to review purchasing records, country-of-origin, and manufacturer details. It is a time-consuming process that most procurement teams are not resourced for.
What Texas Healthcare Providers Should Do Next
The Governor’s directive and the FDA’s underlying guidance together define a clear set of obligations. The question you should answer is how to meet compliance with existing infrastructure.
Here are a few steps for healthcare compliances Texas needs you to meet:
- Map your device ecosystem first: Before any remediation or reporting can occur, you need a complete inventory of every device that qualifies as a cyber device under FDA criteria.
Cross-reference your inventory list with clinical engineering records, DHCP logs, and switch port tables. Devices appearing in one source, but not the others represent direct compliance and security exposure.
- Obtain and cross-reference Software Bill of Materials (SBOM): You need to contact manufacturers to obtain machine-readable Software Bills of Materials for each device.
Once in hand, you have to cross-reference those SBOMs against the NIST National Vulnerability Database and CISA’s Known Exploited Vulnerability Catalog to identify which devices carry unresolved vulnerabilities. Prioritize the Contec CMS8000 and Epsimed MN-120 as they are both specifically named in the Texas directive.
- Establish end-of-life monitoring for device software components: For every device in your inventory, document the manufacturer’s stated support life. This is the period during which security patching will be provided.
Devices approaching or past end-of-support have no remediation path and must be addressed through compensating controls. They are network segmentation, access restriction, and monitoring.
- Integrate cybersecurity events into your workflow: The FDA’s guidance requires that all security vulnerabilities should be part of your Corrective and Preventive Action (CAPA) processes.
Update your quality management processes to ensure that medical device cybersecurity incidents are routed through IT security, clinical engineering, and quality assurance. Document the workflow and the responsible roles before any state-required attestation is submitted.
- Align incident response plans to medical device scenarios: Most existing healthcare incident response plans do not address a compromised patient monitor, or a device used as a network pivot point.
Update your plan to include medical device-specific scenarios. Clinical leadership, biomedical engineering, and legal must be named stakeholders with defined roles.
- Conduct a medical device software testing: The FDA’s postmarket guidance requires evidence of ongoing vulnerability assessment. A manual network penetration test focused on device communication behavior and firmware exposure gives you the documented evidence regulators and auditors will expect.
- Establish a vendor coordination process and document it: The FDA’s guidance framework requires hospitals to maintain active communication channels with device manufacturers for receiving and responding to vulnerability reports.
For any device with a known vulnerability, contact the manufacturer to confirm patch availability, deployment process, and recommended compensating controls. Document every exchange that regulators expect to see as evidence of active coordination, not just reactive response.
How KLEAP can help
KLEAP works with healthcare organizations that carry real regulatory exposure but operate without enterprise-level security infrastructure.
Texas hospitals and health systems navigating this directive fall in that category. From clinical workflows and lean IT teams to the new layer of Texas cybersecurity regulations, we understand the specific pressures Texas healthcare providers face.
KLEAP’s concierge model means your engagement is handled by a dedicated expert who understands both the clinical environment and the security controls regulators expect to see.
There are no handovers, no junior analysts running automated tooling, and no generic report templates delivered at the end of the engagement.
KLEAP not only builds a defensible device inventory, but we also map findings to HIPAA Security Rule requirements and FDA cybersecurity guidance so that your documentation holds up when OCR or a state regulator asks for evidence.
And because the Texas HHSC directive ties device security directly to procurement compliance, we work with your procurement and clinical engineering teams to build a pre-acquisition security review process. So, new devices enter your network already assessed, not discovered during an audit.
If you are a Texas hospital or health system working to build a longer-term security program this directive requires, speak with your KLEAP concierge.