With over 300 hospitals and a rapidly expanding health startup industry, Florida remains one of the most dynamic healthcare ecosystems in the United States.
That growth has also made it a prime target for cyberattacks.
According to a Bridewell report, Florida ranks fourth nationally for healthcare data breaches, with 123 impacted medical centers in 2026 alone. But the numbers get worse from here.
In 2024, the Florida Department of Health suffered a breach that exposed the data of 729,699 individuals, placing it among the 15 largest healthcare provider data breaches in the US that year.
Nationally, nearly 57 million individuals were impacted by large data breaches in 2025. Healthcare has held the top position for the most expensive industry data breach for 14 consecutive years, with the average cost of a healthcare data breach reaching $4.4 million in 2025 as per IBM’s Cost of Data Breach Report.
This is the threat environment that every Florida healthcare organization is operating in right now. Before we examine each attack vector and how to mitigate them, let’s check why the threat is this severe in the first place.
Why Florida's Healthcare Boom Also Increases Its Risks
While the expansion of Florida’s healthcare looks impressive on paper, cybersecurity has a hard time scaling at the same pace. It significantly widens the attack surface.
Every hospital has a set of EHR integrations, patient portals, billing clearinghouses, insurance APIs, and third-party vendors. Each of those connections is a potential entry point. And with Florida’s patient population on the rise, this amplifies the risk.
The patient count combined with the sheer volume of healthcare establishments (13,353 across the state as of 2024) adds to the density of PHI flowing through Florida’s healthcare infrastructure.
Thus, healthcare is not a random target as attackers are aware of the pressure hospital networks are under. The urgency of providing care and the inability to shut systems down without affecting patient care forces healthcare organizations to pay the ransom.
And all these hectic workflows are also the reason why it is slow to detect intrusions. According to an IBM report, the median dwell time for a healthcare breach before discovery is 213 days.
Meanwhile, the average data breach cost of $4.4 million as cited by IBM is not just the ransom amount.
It includes the cost of forensic investigation, OCR civil monetary penalties, class-action lawsuits, remediation roadmaps, and increased cyber insurance premiums. Even the loss of patient trust and organizational reputation is a cost most overlook.
What Are the Attack Vectors Hitting Florida Healthcare the Hardest?
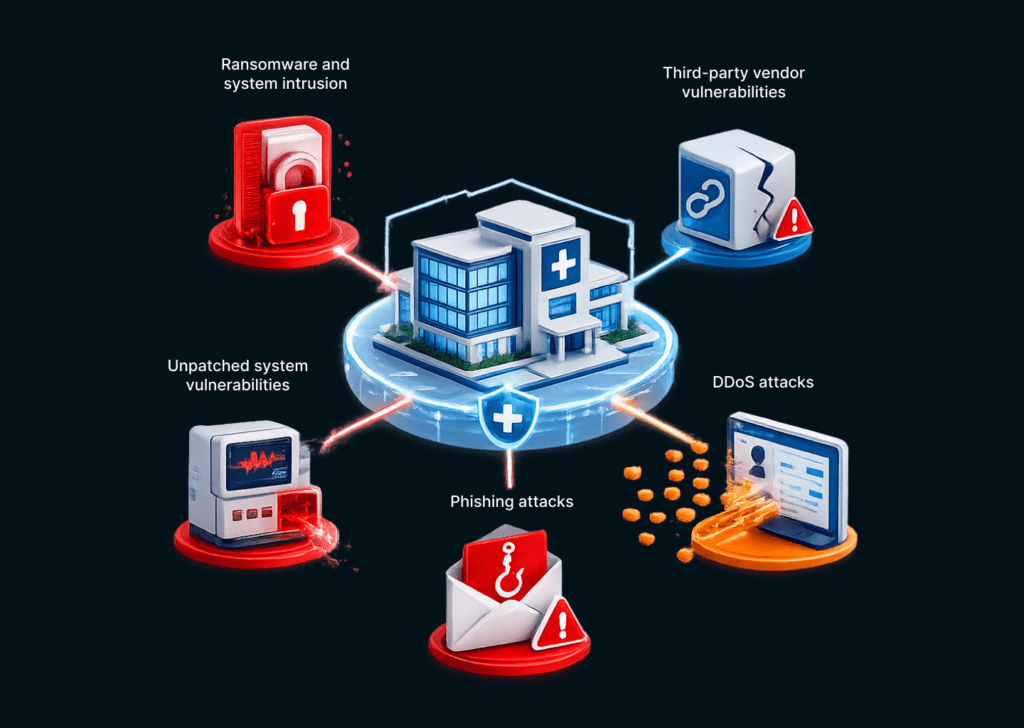
A string of breaches has documented where your Florida healthcare organization is most vulnerable. Understanding which vectors are being used is the first step toward building the defenses against them.
Some of the common attack vectors are:
- Ransomware and System Intrusion: Ransomware is now the leading cause of healthcare data breaches, according to Verizon’s 2025 Data Breach Investigations Report. And for good reason. Healthcare is still the most targeted industry for ransomware. In 2025, there has been a 50% rise in ransomware incidents globally, with healthcare facing approximately 30% of all attacks.
The Florida Department of Health breach in 2024 followed this exact playbook: network intrusion, data exfiltration, and public leak when the ransom could not legally be paid.
Ransomware not only steals your data but also shuts down your access to EHRs, forces care teams onto paper-based processes, and delays procedures. These further delays life-saving care, demonstrating that this is no longer about data, but about direct patient safety.
- Phishing Attacks: Phishing is the most common attack vector, one that is most directly tied to workforce behavior. Phishing attacks are designed to trick you into handing over sensitive information or infecting your system with malware.
It is a common first step for data breaches, ransomware, and similar attacks. A single employee clicking a convincing email is often all it takes. In a Florida healthcare environment with many of them working across multiple locations, often remotely, phishing awareness is a must.
- Third-Party Vendor Vulnerabilities: 65% of healthcare data incidents in 2024 were directly attributed to vulnerabilities within vendor ecosystems. This means, every vendor program, from EHR platforms and billing clearinghouses to medical imaging software and AI transcription tools, anything that has privileged access to PHI presents a potential point of entry.
Most healthcare organizations sign BAAs with every vendor that touches ePHI. But a BAA is no proof of a vendor’s security posture. That can only come from security testing.
- Exploited Vulnerabilities in Unpatched Systems: For the first time in three years, exploited vulnerabilities were identified as the most common cause of healthcare ransomware attacks. It happens when devices are not updated regularly.
A manual penetration test can replicate a realistic attack path. It finds whether an API endpoint is exposed or the network is misconfigured. Knowing a vulnerability exists and understanding whether it is exploitable makes all the difference.
- DDoS Attacks: A DDoS attack uses a network of compromised systems to bombard a target with more traffic than it can handle. Like a ransomware attack, a DDoS attacker may demand a ransom to restore an organization’s operations.
For your Florida healthcare organization running patient portals, telehealth services, and real-time clinical systems, a sustained DDoS attack is a disruption to patient wellbeing.
IT leaders inside Florida healthcare organizations should understand that the question is no longer whether an attack will happen. It is whether the controls in place are sufficient to detect, contain, and survive one.
Why is the 2025 HIPAA Security Rule Update Raising the Security Bar?
In December 2024, HHS published the most sweeping proposed update to the HIPAA Security Rule since 2003. Although the proposed rule is currently under review, Florida healthcare organizations should move toward compliance now before they become rules.
Several of the proposed changes are directly relevant to IT and security leadership:
- Annual Penetration Testing: The Notice of Proposed Rulemaking (NPRM) explicitly proposes mandatory penetration testing at least once every 12 months, and vulnerability scanning at least every six months. This moves pentesting from a best practice to a compliance requirement.
- Mandatory MFA: Multi-factor authentication (MFA) becomes required for all ePHI access points, not just remote access, but all system access, including EHRs, patient portals, and administrative systems.
- Mandatory Encryption: Encryption of ePHI both at rest and in transit should become a required measure.
- Asset Inventory and Network Mapping: Organizations must maintain and annually update their asset inventory and map a network showing ePHI data flows across all systems.
- 72-Hour Incident Notification: Business associates must notify covered entities of the loss of certain relevant electronic information systems and data within 72 hours.
- Business Associate Verification: Covered entities must actively verify that business associates’ security controls are meeting HIPAA requirements and not just collecting signed BAAs and file them.
As new facilities come online in Florida, along with new vendor integrations and tightening the regulatory frameworks, healthcare security programs must evolve.
What Should An Effective Healthcare Security Program Look Like?
While awareness is necessary, it is not enough. The question you must answer is whether your security program is practical enough to reduce risks.
The controls that clos security gaps in your healthcare organization are not complicated. But they require implementation and regular validation.
Here is what effective cybersecurity services Florida healthcare should look into:
- Multi-factor authentication should be on every hospital and vendor account without exception. MFA requires users to provide additional verification, such as a fingerprint scan or a unique code sent to their mobile device, ensuring that only authorized individuals gain access to sensitive information.
As the proposed HIPAA Security Rule update makes MFA mandatory across all ePHI access points, Florida healthcare organizations should invest in MFA not only to stop phishing attacks but also as a future compliance obligation.
- Employees are often the weakest link in an organization’s cybersecurity, making ongoing training crucial. Training sessions should cover topics such as threat identification, best practices for handling sensitive information, phishing, and reporting suspicious activities.
The Florida Department of Health did not lose patient data because of some backdoors in their system. It was employee behavior that made the cyberattack possible. Clicking a link, using a weak password, sharing credentials across systems, all these should be covered in training.
- Encryption technology makes data unreadable format without a decryption key, ensuring that even if unauthorized individuals gain access to the data, they cannot decipher its contents. Under the proposed HIPAA Security Rule update, encryption moves from an addressable specification to a requirement.
Florida healthcare organizations running EHR integrations, patient portals, and billing clearinghouses across multiple environments need to verify encryption is implemented end-to-end. They should not assume it is present based on vendor documents.
- Regular security audits help identify vulnerabilities and weaknesses in a healthcare provider’s system. It is important to involve security professionals and clinical engineering staff in the audit process to ensure that both traditional and connected care workflows are taken into account.
An audit that covers administrative IT but misses the hospital’s medical devices produces an incomplete picture of the security risks. Florida healthcare organizations expanding into new facilities or integrating new service lines need audits to map their actual environment.
- Healthcare providers should implement access controls on connected devices to ensure the security of not only ePHIs but also the credentials such as usernames and passwords that staff use to access the medical device.
Medical devices are increasingly becoming networked and, hence, a target. Florida healthcare with dense device deployments should commit to device-level access control as a requirement.
- As cybersecurity is an ongoing process, continuous network monitoring is becoming a must. Healthcare providers should establish a system for monitoring the network and devices for any suspicious activities or potential vulnerabilities.
The median time before a healthcare breach is detected is 213 days because most organizations are not monitoring continuously. Florida healthcare network should look to mitigate that.
- Penetration testing conducted by external experts is a collaboration that can benefit an organization’s current security measures. It can identify potential weaknesses and provide guidance on implementing the most effective cybersecurity practices.
A penetration test checks whether your controls will hold up against a realistic attack. Since OCR’s corrective action plans are built around documented evidence, a pentest report mapped to HIPAA Security Rule requirements is exactly what it needs.
- HIPAA compliance is a critical aspect of healthcare cybersecurity. Florida health providers must have HIPAA as their foundational compliance framework to root out undocumented risk management, unauthorized access controls, and unregulated system activities.
Building a HIPAA compliance program that adheres to OCR scrutiny means treating it as an ongoing operational discipline with documented, repeatable processes, and not an annual one-time exercise.
How KLEAP Can Help Florida Healthcare Organizations?
KLEAP is a boutique cybersecurity firm built specifically for healthcare and manufacturing SMBs, organizations with real regulatory exposure that cannot absorb enterprise-level overhead.
Our concierge model means that every Florida healthcare organization we work with gets a dedicated expert who scopes the engagement to their specific environment, conducts the assessment manually, and explains every finding to your compliance officer or your board without handoffs in the middle.
For Florida healthcare organizations facing increasing data breaches, the risk of regulatory penalties, and the approaching HIPAA Security Rule update, our engagement typically covers manual pentesting, HIPAA compliance consulting, and web application monitoring.
Healthcare security for any hospital in Florida is not a one-time project. As new facilities come online, as vendor integrations expand, and as the regulatory framework tightens, the security program has to evolve with the organization. We are built to work alongside you as that happens.
If you are involved with Florida healthcare, and you are not certain whether your current security posture would survive an OCR investigation or a targeted ransomware attack, the right step is booking a consultation with us.