Over the past few years, California healthcare has improved public health with longer life expectancy and lower death rates. The state hosts thousands of healthcare providers, organizations, and startups along with hundreds of thousands of caregivers.
And that brings its own cybersecurity challenges.
California ranked second nationally for healthcare data breaches in 2025, with 22.6 million patient records exposed. In 2024, healthcare data breaches surged nearly 200% nationwide (444 in 2024 against 149 incidents in 2023) with California consistently among the most affected states.
In the backdrop of such major data breaches, many organizations still think compliance is about avoiding a heavy fine from regulatory bodies. But in reality, it serves as a structural framework to safeguard your company from cyberattacks.
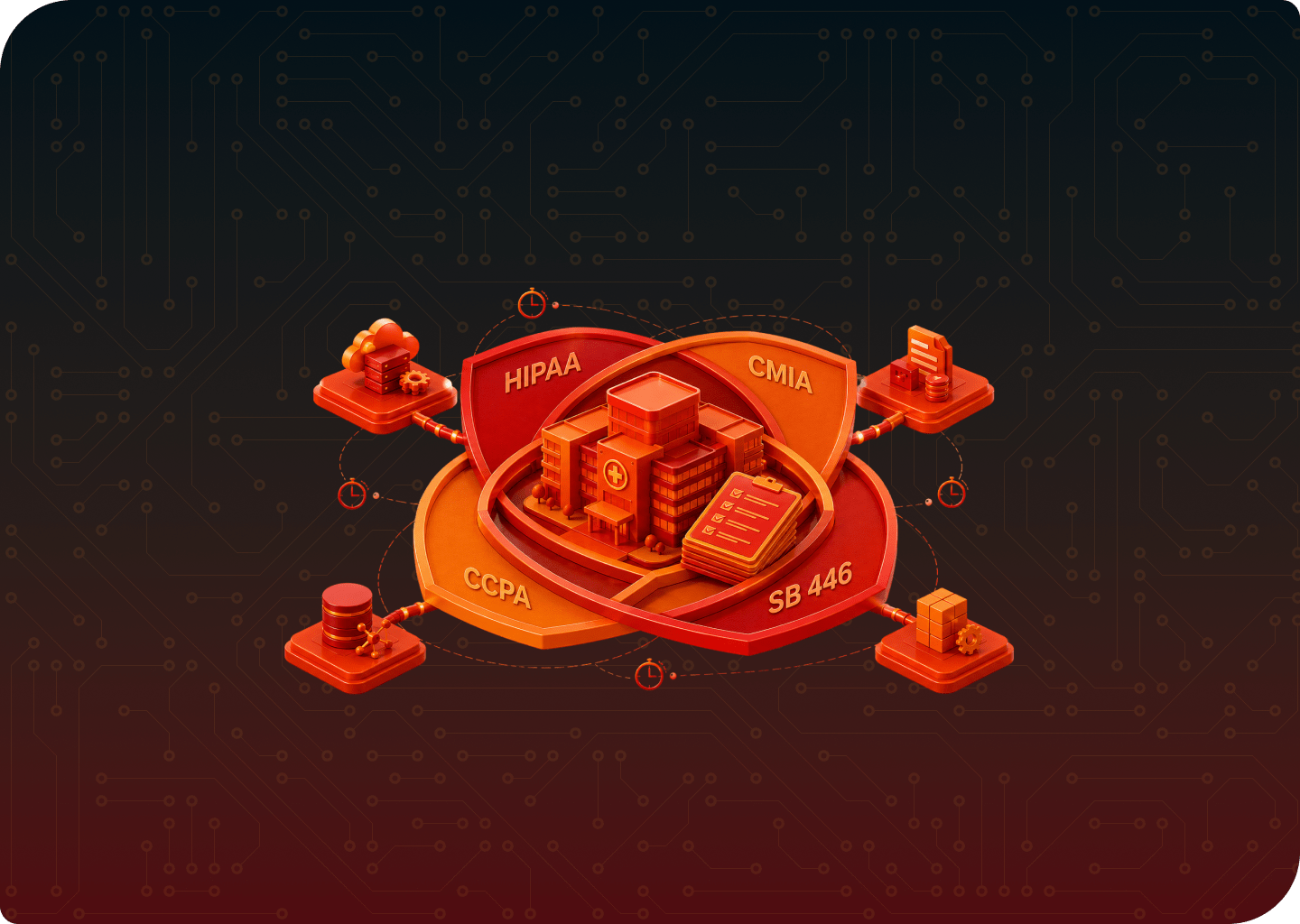
In California, the intersection of federal and state compliances creates a high bar for data protection.
Most healthcare organizations know about HIPAA, which sits at the federal level. At state level, California Consumer Privacy Act (CCPA) and Confidentiality of Medical Information Act (CMIA) also overlap, along with the recent breach notification law SB 446.
Let’s break down each framework before we go ahead into how to prepare for them.
What Makes HIPAA a Federal Mandate?
The Health Insurance Portability and Accountability Act of 1996 (HIPAA) is the federal law governing how individually identifiable health information is used, stored, disclosed, and transmitted.
As a California healthcare organization, you have to determine whether you’re a covered entity or business associate is the first step toward HIPAA compliance.
HIPAA’s Privacy, Security, and Breach Notification rules are especially positioned to protect PHIs. The Privacy Rule establishes standards for when they can be used and disclosed. The Security Rule ensures the confidentiality, integrity, and availability of ePHIs through administrative, physical, and technical safeguards.
Meanwhile, the Breach Notification Rule requires you to disclose to patients if any breach affects their personal data within 60 days.
Achieving HIPAA compliance is non-negotiable for healthcare security in California. HHS Office for Civil Rights (OCR) enforces it as a regulation with fines ranging from a few hundred dollars for unknowing violations to over two million dollars for willful neglect.
Several factors make it a federal mandate:
- Congressional Authority: Healthcare transactions such as insurance claims, electronic billing, and payments cross state lines constantly. That gave Congress the constitutional footing to legislate healthcare data nationally.
- Federal Enforcement: Civil monetary penalties by OCR are assessed at the federal level, and the Department of Justice handles criminal prosecutions for willful violations. As such, no state attorney general can override OCR’s jurisdiction.
- Federal Preemption: If a state law conflicts with HIPAA and is less protective, HIPAA preempts over that. This preemption clause is what gives it true federal mandate status.
- No Geographic Carve-Outs: A covered entity in any state is answerable to the same HIPAA rules, the same OCR, and the same penalty structure. There is no state-by-state variation for California.
What are the requirements under CCPA?
The California Consumer Privacy Act, effective since January 1, 2020, is a state privacy law that gives California residents control over the personal information that businesses collect.
It applies to any for-profit business in California, and your healthcare organization is a part of it.
Many have prioritized HIPAA over CCPA in the past, thinking HIPAA compliance will cover everything. But that is where they are wrong.
There are several categories of data that remain within CCPA’s scope regardless of your organization’s HIPAA status:
- Employee Data: The CCPA’s definition of personal information includes professional or employment-related information. This includes employee records, hiring data, and workplace communications, which are not PHI.
For a California healthcare organization with 100 or more employees meeting CCPA’s revenue thresholds, protecting employee information is a compliance obligation.
- Marketing and Website Data: Patient’s portal activity collected for marketing purposes falls outside the HIPAA. The monitoring is usually done for digital advertising and behavioral study.
Any personal information collected such as email addresses, device identifiers, geolocation data, and browsing behavior falls under this scope.
- Data From Non-HIPAA-Covered Products: Wellness programs, a hospital gift shop, or a consumer-facing app that does not transmit data through standard HIPAA transactions may have products and services that generate personal information entirely outside HIPAA’s scope. But that may fall within the CCPA’s scope.
- Third-Party Licensed Data: Demographic data, social health data, and other information licensed from third parties for analytics is generally not PHI. But it falls under CCPA if it concerns California residents.
The CCPA grants California residents six core rights over their personal information:
- The right to know what is being collected and how it is used.
- The right to delete personal information held by a business.
- The right to opt-out of the sale or sharing of their data.
- The right to correct inaccurate information.
- The right to limit the use of sensitive personal information.
- The right to non-discrimination for exercising any of these rights.
As part of the CCPA, you must publish a privacy policy disclosing what categories of personal information are collected, the sources, the business purpose, and the categories of third parties that receive the data.
You must also provide a mechanism for consumers to submit requests, either by a toll-free phone number or a web form. This also includes responding to those requests within 45 days.
CCPA is enforced by the California Attorney General and the California Privacy Protection Agency (CPPA). Fines run to $2,500 per unintentional violation and $7,500 per intentional violation.
The Act also allows private right of action for California citizens. These are individuals whose personal information is exposed in a breach due to a business’ failure to secure them properly. This is a mechanism that HIPAA lacks.
CMIA Expands Beyond HIPAA
The California Confidentiality of Medical Information Act (CMIA), under California Civil Code §§56 et seq, is the state’s medical privacy law that sits alongside HIPAA rather than replacing it.
CMIA applies to healthcare providers, health care service plans, pharmaceutical companies, and their contractors. Importantly, it also extends to businesses that maintain medical information.
In 2022, CMIA was extended to include health digital services on both mobile applications and websites. Two years later, it was again extended to add reproductive and sexual health application information to the definition of medical information.
For healthcare security in California, CMIA is an obligation even if they are software vendors, wellness apps, or digital health platforms with no BAA and no HIPAA covered entity relationship. It is based on what your product does.
CMIA imposes several requirements that either exceed HIPAA’s standards or operate differently:
- Written Authorization Format: CMIA requires that any written authorization for disclosure of medical information be printed in a minimum of 14-point type, with proper authorization language. HIPAA has no such caveats.
- Electronic Record Audit Trails: CMIA specifically requires that an electronic medical record system automatically record and preserve any change or deletion of electronically stored medical information
This includes the identity of the person who accessed or changed the information, the date and time of access, and the nature of the change made. HIPAA’s audit log requirement is more general and does not specify.
- Sensitive Health Data Segregation: Under the 2024 CMIA amendments, medical information related to gender-affirming care, abortion, and contraception must be logically segregated
HIPAA has no such measures.
- Private Right of Action: Any individual may bring a civil action against any person or entity that negligently releases confidential medical information.
Infamously, HIPAA provides no private right of action. This means a CMIA violation can generate direct patient litigation, not just regulatory action.
As you can see, a control set built purely to satisfy HIPAA compliance will not necessarily satisfy CMIA’s requirements. Those gaps need to be closed explicitly.
SB 446 Tightens California’s Breach Notification Window
Prior to January 1, 2026, California’s Breach Notification Law required you to notify affected residents “without unreasonable delay.” That left it open to interpretation.
HIPAA gave healthcare organizers a 60-day window. And that flexibility gave some operational room. However, SB 446 closes that gap entirely.
Signed into law by Governor Gavin Newsom on October 3, 2025, SB 446 imposes two specific deadlines on any individual or business that conducts business in California and owns or licenses computerized personal data about California residents:
- 30 calendar days from the date of discovery of a breach to notify affected California residents.
- 15 calendar days from the date of notification to submit a sample notification to the California Attorney General, for any breach affecting 500 or more California residents.
This is not a minor scheduling adjustment. For healthcare security teams accustomed to a 60-day federal window, SB 446 effectively cuts the investigation, containment, and notification timelines in half.
HIPAA’s Breach Notification Rule, under 45 CFR §§ 164.400–414, also has different obligations for you by the data breach size.
Breaches affecting fewer than 500 individuals need annual reporting to HHS, and those above that threshold require immediate reporting and an additional notification to the media.
Business Associates also have their own obligations. When a BA discovers a breach of PHI, it must notify the covered entity within 60 days. The covered entity then takes responsibility for notifying affected individuals and the HHS, if it’s not mentioned in the Business Associate Agreement or BAA.
Where HIPAA, CMIA, CCPA, and SB 446 Overlap and Leave Gaps?

As a California healthcare organization, you have one data environment that is governed differently by four different frameworks, depending on the type of data, who is affected, and what caused the incident.
Understandably it is a challenge in 2026. Let’s look at the compliances as they overlap in scope and regulations.
1. CMIA is not an alternative to HIPAA, but an addition.
Both frameworks govern medical information, but CMIA imposes stricter authorization requirements, mandates more audit trails, and creates a private right of action that HIPAA does not.
Your security and compliance program must be calibrated to CMIA’s standards when it comes to these areas as HIPAA lacks these controls.
2. A BAA is not enough to cover vendor risks in California.
CMIA is also relevant to vendor management in a way that dan catch you off guard. A vendor may not handle PHI and thus think it is not a business associate. But it may still be a CMIA contractor under California law.
That means a BAA alone is insufficient. California-specific vendor agreements need to address CMIA obligations independently with CCPA service provider agreements.
3. The CCPA’s HIPAA exemption doesn’t cover everything.
The CCPA exempts PHI collected by HIPAA-covered entities and business associates. It also exempts medical information collected under the CMIA.
But the exemption does not cover everything. Employee records, billing contact data, website visitor data, and consumer behavior data are not PHI, and remain subject to CCPA compliance obligations. It runs simultaneously alongside the HIPAA and CMIA programs.
4. The Breach Notification timelines do not align.
HIPAA allows 60 days from discovery of breach to notify affected individuals. SB 446 requires notification within 30 days with an additional submission to the California Attorney General within 15 days.
If you experience a breach involving both PHI and other personal information, two notification clocks run simultaneously, and the California clock is twice as fast.
5. CCPA gives rights to Californians that HIPAA does not.
In CCPA, affected individuals get a private right of action when non-PHI personal information is exposed in a breach.
For PHI breach, HIPAA enforcement comes into play. It is enforced exclusively by OCR, and patients cannot bring a lawsuit for a HIPAA violation.
6. The de-identification standards differ between HIPAA and CCPA.
Both frameworks allow organizations to use de-identified data, but the standards differ. Data that meets HIPAA’s de-identification standard under the Safe Harbor may not satisfy the CCPA’s de-identification standard.
This is an often-overlooked gap in California healthcare regulation, particularly for organizations running analytics programs on data they believe is fully insulated by their HIPAA compliance posture.
How California Healthcare Organizations Can Meet HIPAA, CMIA, CCPA, and SB 446 Requirements?
Meeting the full California healthcare regulation stack of HIPAA, CMIA, CCPA compliance, and the SB 446 breach notification timeline requires a unified program. The controls that satisfy one framework often partially satisfy another.
Your goal should be to identify where each framework’s requirements diverge and close those gaps. Below is a consolidated compliance action list for healthcare security in California.
- Conduct a multi-framework risk assessment. Start with a documented Security Risk Assessment (SRA) that maps every system, data flow, and vendor relationship against all four frameworks, not just HIPAA.
- Classify your data by framework, not by system. Build a data inventory that separates PHI governed by HIPAA, medical information governed by CMIA, and non-PHI personal information subject to CCPA.
These are three distinct categories with different access controls, retention rules, consent requirements, and breach obligations, which you need to take note of.
- Build your authorization processes to CMIA’s stricter standards.
HIPAA allows written authorizations in general form. CMIA requires that any authorization be printed in a minimum of 14-point type, with proper authorization language, and several other rules that separate it from federal compliances.
- Configure electronic audit trails to CMIA specifications. HIPAA requires audit logs in general terms, but CMIA is more specific.
Any electronic medical record system must automatically record and preserve every change, including the identity of the person who accessed or changed the information, the date and time of the access, and the nature of the change
- Segregate sensitive health data categories as required by CMIA. Under CMIA’s 2024 amendments (AB 352), medical information related to gender-affirming care, abortion and related services, and contraception must be logically segregated from the rest of the patient record, with access restricted to authorized individuals only.
- Identify and address your CCPA compliance obligations for non-PHI data. This includes employee personal information, website visitor data, marketing contact records, and inferences derived from consumer behavior.
Practical steps include publishing a CCPA-compliant privacy policy, building a consumer rights request mechanism, establishing a 45-day response protocol for consumer requests, and reviewing all third-party data sharing arrangements
- Rebuild your incident response plan around SB 446’s 30-day window. If your incident response plan was designed around HIPAA’s 60-day clock, it is already out of date.
- Extend vendor contracts beyond BAA. CMIA binds contractors and vendors independently of whether a BAA exists, provided they create, maintain, or possess medical information.
Vendors who handle non-PHI personal data for the organization need CCPA service provider agreements with restricted use clauses. Review your full vendor portfolio against all three of these contract types
- Implement MFA, encryption, and access controls across all ePHI systems. The proposed 2025 HIPAA Security Rule updates formalize MFA, encryption at rest and in transit, and role-based access control as mandatory requirements.
- Conduct annual workforce training that covers all applicable frameworks. HIPAA requires annual workforce training for any employee who may access PHI.
You must train your healthcare security in California on CMIA’s authorization and disclosure requirements, CCPA’s consumer rights and response obligations, and SB 446’s breach notification timelines
- Conduct manual penetration testing to validate technical safeguards. A documented risk assessment identifies where vulnerabilities may exist. But a penetration test demonstrates whether they can be exploited.
You should scope it to your web applications, APIs, network infrastructure, Active Directory, EHR integrations, and cloud environments
- Document everything and maintain audit-ready records. Maintain current records of risk assessments, penetration test and remediation, workforce training, breach notification exercises, vendor contract reviews, consumer rights request logs (under CCPA), and authorization form audits (under CMIA).
How KLEAP can help?
California healthcare compliance is not a single-framework problem, and not something that a generic checkbox-driven audit process can solve.
KLEAP is a boutique cybersecurity firm that works exclusively with healthcare organizations. For California healthcare organizations navigating HIPAA, CMIA, CCPA compliance, and SB 446 simultaneously, that specialization matters.
The concierge model means every engagement runs through a dedicated expert assigned to your organization. From the first scoping call to the final audit-ready document, one expert stays with you until your operations meet the compliances.
KLEAP conducts manual penetration testing, not automated scans dressed up as assessments. Manual testing validates exploitability in your controls.
Every finding is mapped to the regulatory requirement it implicates, from HIPAA Security Rule and CMIA’s audit trail to the security standards of CCPA enforcement. When OCR or the California AG asks what your controls have and how they hold up against real-world exploitation, you will have the documentation ready to prove them.
KLEAP will help you build programs around HIPAA, while also guiding you for what is needed under CCPA, and CMIA. That means mapping your data environment across PHI, CMIA medical information, and non-PHI personal data subject to CCPA, with distinct controls for each category.
And you will also have an incident response plan around SB 446’s 30-day notification window, not the 60-day HIPAA clock that most teams have integrated into their procedures.
If you are not sure where your HIPAA compliance program ends and where your CMIA and CCPA exposure begins, that is exactly where KLEAP can help.