Michigan’s defense manufacturing sector is growing.
The state has one of the densest Department of War (DoW) supply chain footprints in the country, and there are strict, cybersecurity standards for contractors and sub-contractors handling Controlled Unclassified Information (CUI).
To verify that defense contractors have implemented the cybersecurity controls required to protect CUI, the DoW introduced the first version of the Cybersecurity Maturity Model Certification (CMMC) in 2019.
The updated CMMC 2.0 streamlines the original five-level framework into three levels, each tied to the type of information a contractor handles.
Starting November 10, 2026, Level 2 certification from an accredited CMMC Third-Party Assessment Organization (C3PAO) will be mandatory for getting CUI contracts.
For Michigan manufacturers, this means they have to map their cybersecurity practices to the 110 controls under 14 domains of NIST SP 800-171 Rev. 2 to comply with DoW regulations (DFARS 252.204-7012) and to align with CMMC Level 2 requirements.
Let’s talk about what CMMC Phase 2 requires of manufacturers in the state.
Why Michigan Manufacturers Need to Pay Attention to CMMC Phase 2?
Michigan sits at the center of the U.S. defense manufacturing ecosystem. From aerospace components to precision-machined parts, the state has a long and active relationship with the DoW supply chain.
And the numbers reflect that. In 2024, more than 4,800 DoD contracts valued at $3.21 billion were awarded to companies in Macomb County alone. Those account for 65% of all federal defense contract dollars awarded in Michigan that year.
And the sector is flourishing day by day.
Governor Gretchen Whitmer recently announced a $50+ million Michigan Maritime Manufacturing Initiative partnership with the DoW and Department of Labor. Meanwhile, American Rheinmetall committed $31.7 million to expand its Michigan manufacturing operations.
The growth of Michigan’s defense manufacturing footprint means more companies are entering or deepening their DoW supply chain relationships.
But that also means the increase of opportunity is increasing more scrutiny.
CMMC 2.0 Phase 2 makes it mandatory for manufacturers across the US to have a C3PAO certification if they are handling applicable Level 2 CUI contracts. Most organizations require 6 to 18 months to complete scoping, remediation, documentation, and assessment by an assessor.
So, it is better that you get ahead before November 10, 2026, deadline hits.
However, there is another dynamic that makes the timeline more urgent.
Prime contractors are not waiting for formal Phase 2 enforcement. Many are already requiring subcontractors to demonstrate CMMC readiness before including them in bids, even when it is not formally required yet.
A non-compliant subcontractor can disqualify a prime’s entire proposal. So, it is time to learn what CMMC requires of you.
What Does CMMC Level 2 Require?
As per 32 CFR Part 170, CMMC 2.0 requires documented, defensible proof of cybersecurity posture across 110 security controls from NIST SP 800-171 Rev. 2.
Under Phase 2, assessors will not accept verbal assurances, and you will have to prove that the controls are in place.
The assessor will also look into the remediation measures you have taken when encountering a gap, and both steps need to be documented.
To get a better understanding of the security posture you need, here are the 14 domains housing the 110 controls as mentioned in NIST SP 800-171 Rev. 2:
- Access Control: Who can access what, under what conditions, and with what authentication requirements fall under access control.
- Audit and Accountability: This consists of keeping a log of system activity in a way that enables forensic reconstruction.
- Configuration Management: This documents baseline configurations and controlled change processes.
- Identification and Authentication: MFA requirements, credential management, and session controls are part of this domain.
- Incident Response: This is a tested plan, not just a written one, that assessors look for. It includes documented tabletop exercise records designed to test an organization’s crisis management procedures.
- Maintenance: These are controls over how systems are serviced and by whom.
- Media Protection: Media protection involves physical and logical controls over CUI on portable media.
- Personnel Security: This is the screening and termination procedure.
- Physical Protection: These are the physical access controls for facilities where CUI is processed.
- Risk Assessment: A risk assessment involves periodic evaluation of threats, vulnerabilities, and exposures to identify gaps in your security system.
- Security Assessment: Ongoing monitoring and evaluation of control effectiveness fall under this category.
- System and Communications Protection: Review your network architecture controls to confirm whether CUIs are encrypted in transit.
- System and Information Integrity: Malware protection, security alerts, and flaw remediation are some of the controls under this domain.
- System Protection: It focuses on CUI handling at the boundary level.
For manufacturers running ERP systems, MES platforms, and Active Directory environments, many of these controls have direct implications for how production systems are configured, segmented, and monitored.
The Readiness Gaps That Derail Michigan Manufacturers
Industry data makes the readiness situation clear. Only 9% of contractors report meeting all foundational CMMC requirements.
The gaps that most manufacturing units face are not obscure technical controls. They are the foundational requirements that, if missing, can block certification and additionally cannot be deferred on a Plan of Action and Milestones (POA&M).
Here is what the most common gaps look like in practice, particularly for manufacturing environments:
- Missing or incomplete System Security Plan (SSP): Under CMMC Level 2, the SSP is the primary document your C3PAO evaluates. It must map your entire security environment, including the systems in scope, network architecture, personnel, and how each of the 110 controls are implemented.
Many manufacturers have no current SSP, and some have documents that describe the expected environment rather than the actual one. If the SSP is materially incomplete, an assessor will fail the evaluation.
- Undefined CUI scope: CUI is not simply confidential data. It is a specific category of information designated by the government as requiring protection.
Manufacturers often cannot clearly articulate which systems process CUI, how CUI flows through their network, or where it is stored. Limiting scope through proper CUI identification can reduce the systems that fall under assessment and cut remediation costs significantly.
However, if done poorly, an undefined CUI boundary derails the assessment before it starts.
- MFA failures: Multi-factor authentication is a non-negotiable CMMC control. It is also one of the crucial requirements that cannot be deferred to a POA&M.
Manufacturers operating with shared credentials, legacy systems without MFA support, or remote access configurations that bypass authentication requirements will encounter these as non-negotiables during assessment.
- Untested incident response plans: 38% of contractors do not have a tested incident response plan. Having a plan on paper is not the same as having a tested plan.
CMMC assessors treat an untested Incident Report plan as incomplete. And it is also a control that cannot be deferred to a POA&M.
- Insufficient audit logging and monitoring: Manufacturers often run production environments where keeping a log of records is treated as optional.
CMMC requires audit logs that capture who accessed what, when, and what actions they took. Many ERP and MES systems require deliberate configuration to meet this standard, and even then, the data must be documented and reviewed.
- Mismanaged POA&Ms: POA&Ms are tightly constrained under CMMC Level 2. They are only permitted for certain low-point requirements, with a 180-day window.
Several foundational controls cannot be deferred at all. Treating a POA&M as a general safety net for unprepared controls not only puts your cyber security at risk but also leads to CMMC rejection.
A Practical CMMC Readiness Roadmap for Manufacturers
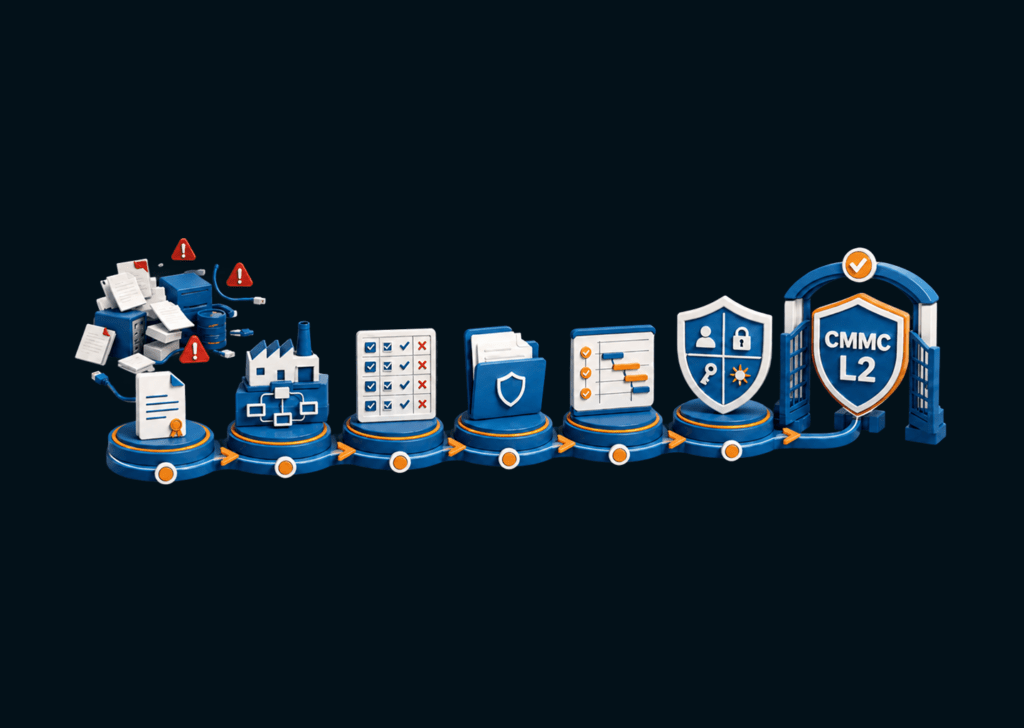
There is no shortcut to a C3PAO assessment. But there is a logical sequence that reduces wasted effort and avoids costly remediation under pressure.
This CMMC readiness guide shows you the steps you should take to be CMMC Level 2 ready:
Step 1: Determine your CMMC level
Review your contracts in reference to CUI, DFARS 252.204-7012, or CMMC Level requirements.
If your contracts involve manufacturing components, technical drawings, specifications, or other design data delivered under a DoD contract, CUI is likely present.
Step 2: Identify and scope your CUI environment
Map every system, network segment, and workflow that stores, processes, or transmits CUI.
Identify which cloud services, ERP modules, file shares, and collaboration tools are in scope. Limiting scope at this stage directly limits the cost of remediation and assessment.
Step 3: Run a NIST SP 800-171 gap assessment
Evaluate your current controls against all 110 requirements and calculate your current SPRS score. Identify which controls are fully met, partially met, and not met.
This baseline tells you how much remediation remains before a C3PAO assessment is viable.
Step 4: Build your System Security Plan
The SSP documents your security environment as it actually is. This includes every tool, every access pathway, and every control.
A well-organized SSP reduces assessment duration and cost. It is the first document assessors evaluate.
Step 5: Develop your POA&M for genuine gaps
For controls that cannot be fully implemented before assessment, document a prioritized remediation roadmap with timelines and ownership.
Reserve the POA&M for controls where deferral is actually permitted, not as a backburner for unaddressed requirements.
Step 6: Remediate high-point controls first
Prioritize controls based on the Supplier Performance Risk System (SPRS) points. SPRS is the DoW’s primary database for verifying contractor compliance. The baseline score is 110, and each unmet control deducts 1, 3, or 5 points depending on its security weight.
Unmet controls include MFA, encryption, incident response, and access control, as these cannot be deferred to a POA&M. Fully implementing these before assessment is another set of non-negotiables.
Step 7: Schedule your C3PAO assessment
C3PAO availability is finite, and the pool of available assessors shrinks as Phase 2 enforcement draws closer.
Get on an assessor’s schedule early, even before remediation is complete, to give yourself a firm deadline and reduce the risk of being unable to bid on contracts simply because no assessors are available in time.
How KLEAP can help?
KLEAP provides manual penetration testing and compliance advisory services purpose-built for manufacturers navigating CMMC compliance.
We are not a C3PAO. We are the firm that gets you assessment-ready before one arrives.
Michigan manufacturing environments, such as Active Directory, ERP integrations, legacy systems, and remote access configurations, carry specific security patterns that general-purpose compliance tools miss.
KLEAP follows a concierge model where our engagements are led by security experts from start to finish with hands-on experience in manufacturing infrastructure.
We do not run automated scans and call them penetration tests. Every engagement involves manual testing, documented findings, and clear remediation guidance tied directly to the NIST SP 800-171 control families your C3PAO assessor will evaluate.
Our Michigan CMMC services cover the full pre-assessment readiness lifecycle, providing gap assessments, CUI scoping and data flow documentation, SSP development, POA&M structuring, and remediation verification to confirm that controls you have implemented satisfy the specific assessment objectives in NIST SP 800-171 Rev. 2.
KLEAP can scope your environment and identify the specific gaps standing between you and a successful CMMC Level 2 certification in one call.