Defense manufacturers build their portals as convenience layers; a fast way to accommodate a prime contractor’s file exchange requirement, or to let suppliers pull orders without clogging up email. Safe to say, they were not designed with compliance boundaries in mind.
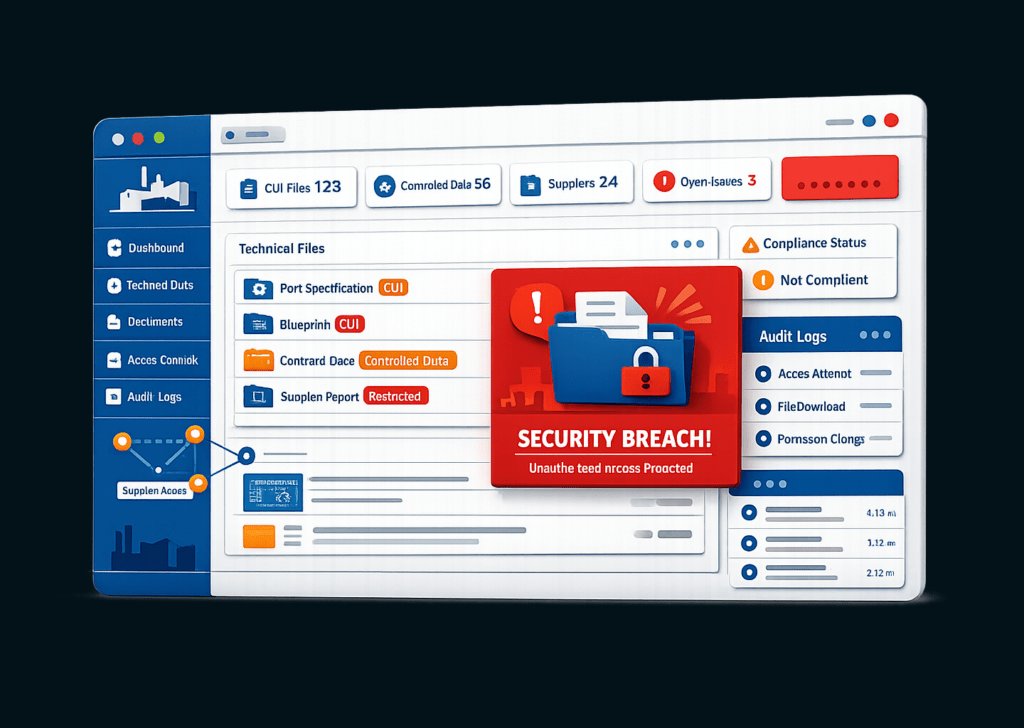
But CMMC readiness is already moving beyond just the internal network. Supplier portals, order management platforms, and technical data exchanges are all active Controlled Unclassified Information (CUI) exposure points under CMMC 2.0.
If your cloud-hosted portal touches CUI, it falls within your CMMC assessment scope, and a FedRAMP-authorized cloud does not automatically make it compliant.
CMMC 2.0 enforcement began on November 10, 2025, with Phase 1 active across new DoW solicitations and contracts. Phase 2, i.e., mandatory Certified Third-Party Assessment Organization (C3PAO) assessments for most Level 2 contracts begin in November 2026.
Most organizations will need six to twelve months to prepare for a C3PAO assessment.
Which means manufacturing services using cloud-hosted portals need to urgently understand what qualifies as CUI, how cloud providers fall inside or outside the assessment boundary, and what controls an assessor will verify.
What Is CMMC & Does Your Manufacturing Portal Fall Under It
The Cybersecurity Maturity Model Certification (CMMC) is the Department of War’s (DoW; previously, DoD) framework for verifying that defense contractors have actually implemented the cybersecurity controls required to protect sensitive defense data.
What is CMMC designed to protect?
Controlled Unclassified Information or simply CUI.
CUI is government-created or government-owned data that requires safeguarding under federal law. It’s sensitive but not classified.
For defense manufacturers, it includes engineering drawings and technical specifications, export-controlled technical documentation, manufacturing process data, and program-related correspondence containing design or performance details.
Documented exposure points in manufacturing include shared engineering drives, CNC machines storing cached part programs, work instruction systems displaying drawings, and supplier portals exchanging technical data with primes and sub-tier partners.
Any portal that processes, stores, or transmits CUI falls within the CMMC assessment scope, regardless of how occasionally it handles that data or how few users touch it.
Most manufacturers handling CUI will require CMMC Level 2 certification, which maps to all 110 security requirements in NIST SP 800-171 Revision 2.
There is no reduced requirement for cloud-hosted systems. Manufacturing compliance also carries a flow-down obligation: if you share CUI with sub-tier suppliers through a portal, your compliance obligations extend to that exchange.
Does Your Cloud Portal Automatically Meet the CUI Requirements Under CMMC
No. This is the most consequential misunderstanding in the CMMC program for manufacturers moving CUI into cloud-hosted environments.
Under DFARS clause 252.204-7012, any cloud service provider that processes, stores, or transmits CUI must meet FedRAMP Moderate authorization or meet security requirements equivalent to the FedRAMP Moderate baseline. That requirement is verified through the FedRAMP Marketplace, and equivalency requires 100% compliance with the FedRAMP Moderate control baseline.
Two failure patterns appear regularly in manufacturing environments.
The commercial version trap. AWS and Microsoft Azure are FedRAMP authorized but only their government offerings: AWS GovCloud and Microsoft Azure Government. A portal running on a standard commercial subscription is not in a FedRAMP-authorized environment. The government version must be specifically procured. Most contractors who didn’t ask for it don’t have it.
The “inherited compliance” trap. Some cloud vendors claim FedRAMP equivalency because they run on AWS or Azure infrastructure. The DoW has addressed this directly: a CSP that inherits some FedRAMP controls from an underlying platform but does not independently satisfy 100% of the required controls does not meet FedRAMP Moderate Equivalency. A gap of even a few controls counts as a failed assessment.
The Shared Responsibility Model makes this problem larger. FedRAMP authorization covers the cloud platform, not your use of it. Access management, logging policy, and portal security configurations remain your responsibility. FedRAMP reduces scope. It does not eliminate your obligations under CMMC.
Which NIST 800-171 Controls Apply to Your Portal & Where Do They Typically Break
All 110 NIST 800-171 controls apply to any in-scope system. For a cloud-hosted manufacturing portal handling CUI, four control families carry the most assessment risk.
| Control Family | What It Requires | Where It Typically Breaks |
| Access Control (AC) | Role-based access, least privilege, session restrictions for all users who can reach CUI through the portal. | Supplier-facing access configured too broadly. Stale accounts left active after engagements end. No session timeout enforcement. |
| Identification & Authentication (IA) | MFA for all accounts, privileged and non-privileged, that access CUI systems. Control 3.5.3 applies to every user, not just administrators. | Portal authenticates through a third-party identity provider that doesn’t enforce MFA. Shared service accounts used for supplier logins. |
| System & Communications Protection (SC) | Encryption of CUI in transit (TLS 1.2 minimum) and at rest. Boundary protection between the CUI environment and other systems. | TLS 1.0 or 1.1 still accepted on portal endpoints. Insufficient boundary between the portal and the broader corporate network. |
| Audit & Accountability (AU) | All CUI access logged with user identity, timestamp, and system accessed. Logs protected from unauthorized modification and retained per defined policy. | Logging enabled at the platform level but not configured to capture portal-specific events. No defined retention period documented in the SSP. |
The pattern is consistent across all four families. Controls exist at the platform level but not at the implementation level.
A portal can sit on a FedRAMP-authorized cloud, have MFA as a feature, use TLS by default, generate logs automatically, and still fail assessment because none of those configurations were verified, documented, or tested against what the SSP claims.
An assessor is not evaluating what your vendor offers. They are evaluating what you have implemented and can prove.
Most Defense Industrial Base (DIB) contractors claim DFARS compliance through self-assessment, but only a limited few have completed assessments that validate their actual operational security posture.
How Do You Define an Assessment Boundary When a Web Portal Is the Entry Point for CUI
Every system, person, and process that touches CUI falls within the CMMC assessment boundary. Bringing your entire enterprise network into CMMC scope can cost two to three times more than confining requirements to a targeted, isolated environment.
So, the most effective approach for manufacturers with cloud-hosted portals is a CUI enclave, i.e., a defined, technically enforced environment where CUI is processed, stored, and transmitted, isolated from the broader corporate network.
Finance, HR, general operations, and shop floor systems with no contact with defense contract data remain outside the boundary.
The key distinction that assessors check for is that the boundary must be technically enforced through firewalls, segmentation, access controls, and monitoring.
For cloud-hosted manufacturing portals, three enclave configurations are most common:
- a FedRAMP-authorized cloud environment (AWS GovCloud, Azure Government, or M365 GCC High) hosting the portal and all CUI workflows;
- a VDI-based model where users access the portal through a virtual desktop, so CUI never reaches the local device;
- and a hybrid model connecting a cloud-hosted portal to specific on-premises systems while keeping the broader corporate environment isolated.
Regardless of model, the enclave boundary must be documented in the System Security Plan (SSP). It must specify which systems, users, and applications are inside the enclave, how the boundary is technically enforced, and how CUI is prevented from crossing into out-of-scope systems. The network diagram must reflect the environment as it actually operates.
What Does CMMC Readiness Looks Like Before a C3PAO Shows Up
CMMC readiness is not about a license purchase or a platform subscription because auditors don’t score what you purchased. They evaluate how you operate.
For a manufacturing organization preparing a cloud-hosted portal for a Level 2 assessment, readiness follows a specific sequence.
Start with the CUI data flow. Map where CUI enters your environment, how it moves through the portal, who touches it, and where it exits. If portal users download drawings to local devices, those endpoints may be in scope. If audit logs sit in a shared environment alongside non-CUI systems, that infrastructure likely is too. The map determines the boundary. The boundary determines everything else.
Build the SSP before remediation. The SSP must reflect the environment as assessed. Documentation written retroactively produces mismatches that are visible to assessors.
Treat the Plan of Action and Milestones (PoA&M) as a required document. It should document unimplemented controls with defined owners and timelines. Having a PoA&M will not disqualify an organization, but having undocumented gaps with no ownership will.
When a C3PAO assesses your portal, they will request configuration exports. They will verify that MFA is enforced at the identity provider level, check TLS settings against actual endpoint configuration, and test whether the enclave boundary behaves the way the SSP describes.
Manufacturing compliance for cloud-hosted portals requires someone who understands both the regulatory standard and the specific environment where CUI lives.
KLEAP conducts manual gap assessments anchored to CUI data flow, validates your enclave boundary, and builds SSP documentation that reflects the environment that will actually be assessed.
Fewer than 100 C3PAOs currently exist for over 80,000 organizations needing assessments. Organizations that act now will be able to secure assessment windows before demand concentrates around the November 2026 Phase 2 deadline.
If you’re on the lookout for a reliable security and compliance partner that understands the nuances within the US manufacturing industry, reach out to us.
