This blog explains why HIPAA compliance and security work differently for dental support organizations, how common attack paths and vendor exposure create risk across locations, what OCR and HIPAA actually require from DSOs, and what year-round audit readiness should look like in practice. It also shows why a concierge model helps keep compliance current as the organization grows.
Dental support organizations (DSOs) do not face the same security and HIPAA compliance pressure as a single-site dental practice. Many DSOs fail to grasp the size or scope of their attack surface as they expand into new locations, users, tools, vendors, and patient records.
OCR had reported a nearly 300% increase in ransomware hacking cases in 2023, and the American Dental Association (ADA) reported in 2024 that hacking has accounted for more than 80% of large breaches since 2021.
That same year, ADA also reported that the Change Healthcare cyberattack disrupted dental practices’ ability to send electronic claims and attachments to insurers, showing how fast a third-party breach can affect day-to-day care and revenue workflows.
What are dental support organizations, and why do they need HIPAA compliance?
DSOs help dental practices scale by centralizing business functions such as billing, staffing, procurement, technology, and operational management across multiple locations.
Their HIPAA compliance is trickier because ePHI, user access, vendors, and workflows are spread across a larger network, which makes it harder to maintain consistent safeguards, clear oversight, and audit-ready evidence everywhere.
A larger operational footprint creates both security and coordination problems. One location may follow access rules closely, while another still has unmanaged vendor access or runs outdated software.
A central team may assume controls are in place, but HIPAA compliance breaks down when the operating reality across locations is inconsistent. This is where HIPAA compliance audits for dental support organizations sometimes fail to uncover gaps buried inside the network of teams, systems, and third parties.
ADA states plainly that dentists are required to be HIPAA compliant, and HIPAA’s Security Rule requires administrative, physical, and technical safeguards to protect ePHI.
That means DSOs need an operating model to manage regulated data across a distributed environment, something a basic IT support model cannot achieve.
The real challenge is always knowing where ePHI sits, who can access it, which vendors touch it, and whether safeguards hold across every supported location. That is also where HIPAA compliance BAA issues start to matter more, because third-party relationships multiply as the organization grows.
What Kind of Cyberattacks Do Dental Support Organizations Keep Facing?
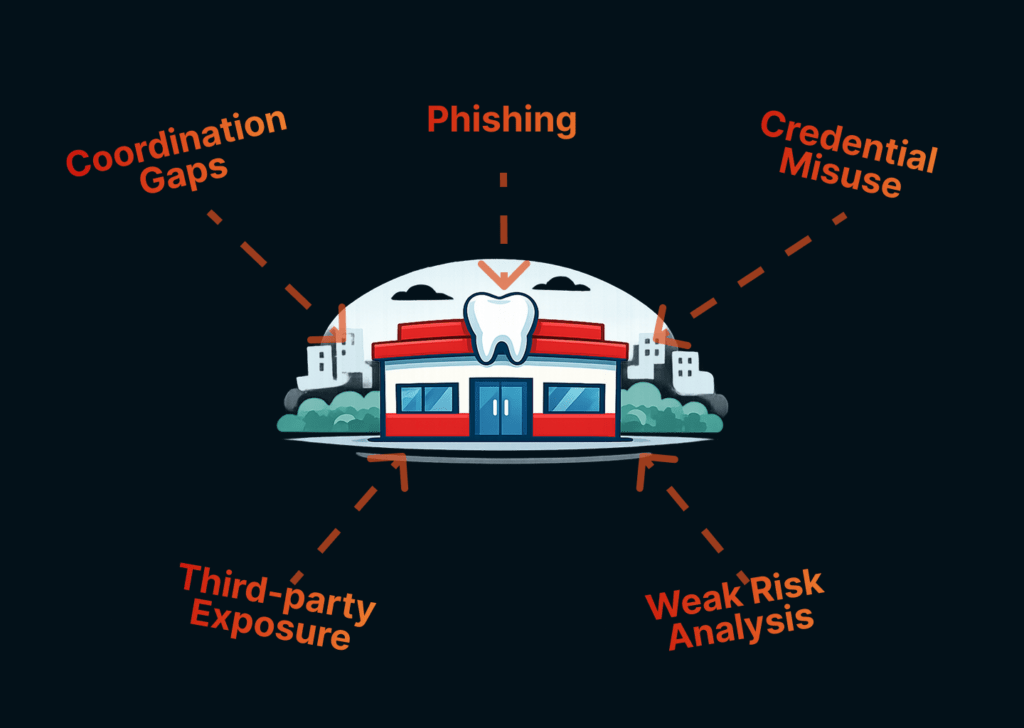
It usually starts with a basic failure point, such as a phishing email, credential misuse, or an unpatched system, and then spreads because access, users, and systems are distributed across multiple locations.
Multiple threat analyses consistently show social engineering accounts for almost 70% of breaches, with technical vulnerabilities making up the rest. These attacks particularly target healthcare providers like DSOs, ambulatory surgery centers (ASCs), and critical access hospitals (CAHs).
Third-party vulnerabilities further compound risk for DSOs because ransomware and other disruptions can originate from external billing platforms, software vendors, and connected services.
At the same time, OCR’s Risk Analysis Initiative has underscored that most large-breach investigations reveal a lack of compliant risk analysis, which means the problem is often not only the attack itself but also the organization’s weak understanding of where risk sits.
HHS’s OCR settlements show a clear pattern through 2024 and 2025: multiple settlements tied to ransomware, phishing, and broader Security Rule failures across healthcare organizations.
A March 2025 stakeholder letter citing 2024 breach research says organizations with worsening security staffing shortages faced an average of USD 1.76 million more in breach costs, and that 53% of organizations reported a critical lack of skilled security workers in 2024, up from 42% the prior year.
This is why HIPAA audit-readiness for dental support organizations must move beyond policy review and account for how attacks actually infiltrate, spread, and disrupt the business in practice.
What HIPAA Compliance Requires from a DSO
The HIPAA Security Rule requires administrative, physical, and technical safeguards to protect ePHI, and HHS’s guidance makes clear that risk analysis is a core part of that requirement.
That means you’ll need provable oversight to pass a HIPAA compliance audit.
Written asset inventories, network maps, more specific risk analysis, and annual verification by business associates that prove technical safeguards are in place.
OCR has repeatedly tied enforcement to failures in the basics:
- incomplete risk analysis
- weak risk management
- missing evaluations after operational change
- weak handling of third-party access to ePHI
Past OCR enforcement has also included failures to define and enforce required ePHI safeguards in business associate agreements (BAAs).
This is where HIPAA compliance BAA issues become more important for dental support organizations. ADA explains that a business associate is a person or entity that performs a function or service for a covered entity and involves the use or disclosure of PHI, while HHS states that covered entities must impose specified written safeguards on PHI in the business associate contract.
For a DSO, that means HIPAA compliance also depends on whether vendors, platforms, consultants, billing partners, and other outside service providers are properly identified, contracted, and reviewed.
Dental support organizations need a healthcare compliance solution that can keep risk analysis current, vendor oversight structured, and evidence retrievable across a distributed environment. That is the only way KLEAP or any serious compliance partner can make HIPAA readiness real instead of assumed.
What DSO HIPAA Audit Readiness Looks Like
Audit readiness between assessments must stay active in four areas: risk, access, recovery, and vendors. It cannot function as an annual review cycle while locations, users, tools, and third-party relationships keep changing.
- Risk Analysis Must Stay Current
Apart from setting up an internal audit cadence, new locations, new remote access paths, new software, or new vendor partnerships should trigger a review.
- Provable Identity & Access Management
HIPAA compliance depends on producing evidence that MFA, user access reviews, and credential discipline are actually functioning across supported locations.
- Backups & Recovery Must Be Tested
HHS is clear that backups alone are not enough. DSOs must ensure they can recover from backups, conduct periodic test restorations, consider offline backups, and maintain contingency planning for security incidents.
- Vendor Risk Must Stay Documented
ADA notes that examples of business associates include consultants, attorneys, and tech vendors that perform services involving PHI for a covered dental practice. A business associate’s subcontractor with access to PHI is also a business associate.
Why DSOs Need a Concierge for Year-Round HIPAA Compliance
Dental support organizations need a model that keeps HIPAA compliance active as locations, vendors, systems, and evidence requirements keep changing.
KLEAP’s concierge approach is built around that exact problem: turning compliance into a roadmap with ownership, cadence, and an evidence trail that stays current across your entire operation.
Keep HIPAA compliance current, provable, and easier to sustain year-round before the next audit or incident forces the issue.