ISO 27001 compliance can create a false sense of security in manufacturing when certification is driven by policies, risk registers, and audit artifacts rather than operational validation. In this blog, we explain where the security gap forms, why certified manufacturers still fail to prevent real attacks, and how to bridge compliance to resilience using OT security guidance from NIST SP 800-82 and industrial security practices embedded in ISA/IEC 62443.
ISO 27001 compliance is built to define how you establish, implement, maintain, and continually improve an information security management system (ISMS). It’s a management standard. It tells you how to run the program.
It does not guarantee you have validated every real attack path across a modern manufacturing environment. That distinction matters both on factory floors and in office-only environments because manufacturing cybersecurity includes systems and devices that interact with the physical world.
NIST’s Operational Technology (OT) security guidance makes this explicit: OT cybersecurity must account for unique performance, reliability, and safety requirements. This is also why manufacturers increasingly need to complement ISMS compliance with industrial-focused security approaches like the ISA/IEC 62443 standards, which specifically define requirements and processes for securing industrial automation and control systems.
- Audit-ready means your ISMS is documented, risks are logged, processes exist, and you can show evidence that matches the standard’s requirements.
- Attack-ready means you have tested whether your actual environment can resist lateral movement, contain breaches, and recover operations under pressure.
In this blog, we get specific about what a typical ISO/IEC 27001 certification tends to resolve and what it tends to miss in real manufacturing environments, especially where IT and OT meet.
What ISO 27001 Compliance Reveals About Your Cybersecurity Posture
Jointly published by the International Organization for Standardization (ISO) and the International Electrotechnical Commission (IEC), a typical ISO 27001 audit is very good at assessing and confirming that your data management and security systems exist.
It checks whether your ISO/IEC 27001 controls are defined, implemented, maintained, and improved through documented processes and evidence trails. However, the manufacturing problem starts when this audit lens becomes the whole lens.
The factory floor is a physical environment with connected systems, production constraints, and an extremely low tolerance for downtime. This is where an “audit mirage” forms: you can pass ISO 27001 compliance checks, but your operational security stays compromised.
What the audit trail captures well
- Policy and governance structure.
- Risk assessment processes and registers.
- Asset inventories and documented responsibilities.
- Internal audit rhythm and management reviews.
What it can miss on the factory floor
- Can an attacker move laterally from IT to OT or between OT zones?
- Are production networks segmented in a way that holds under scrutiny?
- How is remote vendor access controlled and monitored in operational systems?
- What happens when a plant system must keep running but is partially compromised?
This is why industrial security frameworks exist alongside ISMS standards.
The ISA/IEC 62443 series of standards is designed specifically for industrial automation and control systems, defining requirements and processes to maintain electronically secure IACS and bridge the gap between operations and IT, as well as process safety and cybersecurity in manufacturing.
From ISMS Documentation to Actual Attack-Path Validation
ISO/IEC 27001 helps you build an ISMS that is defined, operated, reviewed, and improved. But manufacturers need an extra layer that answers one question auditors don’t consistently test:
Can an attacker exploit security vulnerabilities in your operations?
Because the bar for security validation has shifted from certified to provable, to answer the question above, manufacturers need to know what a security assessment should cover to stay compliant with evolving security standards.
Governments and regulators are tightening security expectations around risk management and accountability, like the EU’s NIS2 framework that expands cybersecurity obligations across critical sectors and raises enforcement pressure.
On the supply chain risk management side, NIST’s SP 800-161r1 focuses on continuous practices like monitoring and responding across dependencies, which demands traceable, up-to-date security proof. And in contractor ecosystems, the DoD guidance for CMMC states it bluntly: to verify and validate practices.
Here’s what attack-path validation looks like in conjunction with ISO documentation.
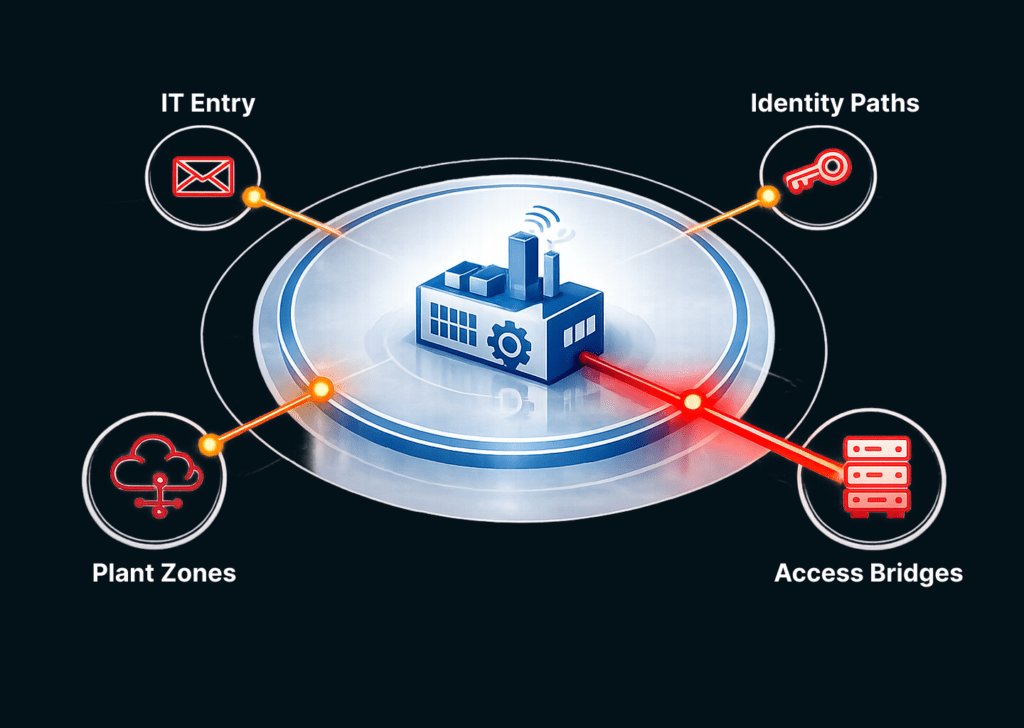
Keep your ISMS scope, but stress-test it against real-world attack patterns:
- IT entry points (email, VPN, SaaS, endpoints)
- identity pathways (shared accounts, service accounts, vendor credentials)
- connectivity pathways (IT to OT bridges, jump servers, remote access tools)
- plant zones (where segmentation should contain spread)
Examples of mapping for validation:
- where privileged access exists and where it’s shared
- where logs originate and how fast they’re reviewed in practice
- where segmentation is enforced, not just documented
- whether recovery works end-to-end for operational dependencies
Attack-path validation should test:
- Can a foothold in IT reach plant systems?
- If one zone is compromised, does segmentation contain it?
- Are there any segments where one compromised device infects many?
Access validation for vendors should include:
- time-bound access, not permanent
- unique identities, not shared accounts
- monitored sessions with reviewable artifacts
- clear offboarding and credential rotation
Prove recovery through:
- restore order of dependencies
- ability to rebuild critical services
- ability to operate safely in degraded mode
- evidence artifacts that show recovery capability
Turn validation into recurring evidence with:
- validation notes
- segmentation evidence
- access review artifacts
- vendor access logs
- recovery test outputs
- exception registers with compensating controls
This way, manufacturers can comply with ISO 27001 while building operational resilience through repeatable validation of their security measures.
Close the Gap Between Compliance & Operational Security with KLEAP
ISO/IEC 27001 gives manufacturers a way to run an information security program that is defined, operated, reviewed, and improved. The gap forms when the program is optimized for the ISO 27001 audit cycle, while real risk lives in operational pathways across IT and OT.
But spotting and plugging those gaps requires redirecting resources and specialized personnel that most manufacturers lack in-house. They need someone to run the workflow without disrupting operations.
That’s where we simplify the security compliance readiness for manufacturers through a guided, concierge-style approach.
KLEAP supports manufacturing teams by:
- translating ISO 27001 compliance into a scoped, plant-aware validation plan.
- mapping ISO 27001 controls to real enforcement points across IT/OT pathways.
- building a continual and repeatable provenance system tied to the audit cycle.
- running periodic attack-path validation so certification aligns with operational resilience.
This helps you actually reap the benefits of the ISO 27001 certification. You not only stay audit-ready, but also your systems become harder to compromise and recover faster. If you’re looking for a reliable compliance partner: