In this blog, we explain why HIPAA compliance in 2026 is shifting from policy-heavy checklists to proof of real security outcomes. Learn how KLEAP simplifies HIPAA readiness by speeding up security reviews and lowering operational disruptions, making healthcare cybersecurity initiatives defensible when audit pressure hits.
HIPAA compliance expectations are shifting toward more rigorous cybersecurity hygiene and demonstrable execution. The clearest signal is that the Department of Health and Human Services (HHS) has proposed updates to the HIPAA Security Rule to strengthen cybersecurity initiatives for ePHI and better address evolving threats to the healthcare sector.
At the same time, OCR’s 2024–2025 HIPAA Audit Program is specifically reviewing selected Security Rule provisions most relevant to hacking and ransomware attacks. This shows that the HIPAA compliance audit is starting to account for verifiable evidence that safeguards operations and can withstand real incidents.
The notice of proposed rulemaking (NPRM) published in the Federal Register points to how healthcare cybersecurity teams must address compliance to better protect the confidentiality, integrity, and availability of ePHI in the current environment.
So, HIPAA compliance, in practice, now requires a repeatable evidence-and-validation workflow that keeps HIPAA readiness intact even when audits, insurers, or incidents arise.
What Is HIPAA Compliance?
If you strip the legal language away, complying with the Health Insurance Portability and Accountability Act in 2026 comes down to your ability to consistently protect ePHI and prove it.
HIPAA has always required safeguards for the confidentiality, integrity, and availability of ePHI. What’s changing is how often healthcare organizations are being asked to demonstrate, with proof, that those safeguards are real, current, and operational. HHS’s proposed Security Rule updates are a signal in that direction.
So, when we say “proof,” we mean the things that survive scrutiny:
- A current risk analysis that actually reflects how ePHI flows across systems and vendors.
- Evidence that access controls, monitoring, and backups are in place and tested.
- Incident readiness that goes beyond an IR document and shows recovery capability, especially for ransomware scenarios.
Here’s the simplest way to explain HIPAA readiness – your policies explain intent. Security remediation evidence proves execution. Validation proves the evidence is trustworthy.
Why Are Healthcare Cybersecurity Teams Being Asked to Show More?
It’s happening because evolving cyberthreats within healthcare are creating pressure from three directions at once.
- Regulators are testing ransomware-relevant scenarios.
OCR’s 2024–2025 HIPAA Audit Program is targeting Security Rule provisions “most relevant to hacking and ransomware.” That changes how a HIPAA compliance audit feels on the ground. You’re not only asked what policy you have. You’re asked what’s implemented, how it’s monitored, and what evidence you can produce quickly.
- The Security Rule itself is being modernized.
HHS has proposed updates to strengthen the HIPAA Security Rule to better address evolving cybersecurity threats to ePHI. Even before any final rule, expectations are moving toward clearer, more operational controls and demonstrable safeguards. That raises the bar for HIPAA compliance maturity.
- Risk analysis is now a must-have.
OCR keeps reinforcing risk analysis as foundational through guidance and enforcement focus, and it expects it to be accurate, thorough, and maintained as environments change. For growing healthcare organizations adding new apps, cloud services, and vendors, that means HIPAA readiness depends on keeping the risk analysis tied to a remediation backlog and an evidence trail.
The problem is that conventional HIPAA compliance programs were built for documentation.
Where Current HIPAA Compliance Initiatives Fail
The most common failure points that show up during an audit or ransomware scenario stem from not treating HIPAA compliance like an operating system: ownership, cadence, evidence, and validation.
Teams run a risk analysis once, file it away, and keep moving. OCR’s guidance expects a risk analysis to be accurate and thorough, and the reality is you must maintain it as systems, vendors, and workflows evolve. If risk analysis is not tied to a remediation backlog, it fails to become a security driver.
Traditional programs often label ownership as “IT” or “Security.” HIPAA readiness needs named owners per control area and per system, plus acceptance criteria that define what “fixed” means. Otherwise, you end up with fixes that cannot be proven and controls that cannot be defended.
Evidence is scattered and hard to retrieve. It lives across ticketing tools, EHR admin consoles, identity providers, spreadsheets, vendor portals, and email threads. OCR’s audit focuses on areas relevant to hacking and ransomware, i.e., you will be asked to prove operational evidence.
A written incident response plan is not incident readiness. Readiness means you can detect, contain, and recover with known roles and known artifacts. HHS’s ransomware guidance makes it clear that ransomware is a major threat and that HIPAA-regulated entities should implement safeguards and be prepared to respond and recover. This expectation creates a gap for compliance programs that stop at policy and training.
Finally, a lot of HIPAA compliance programs are driven by third-party templates. That feels efficient until you need to show the provenance of implementation. OCR’s own audit report flagged template policy manuals without evidence of entity-specific review or implementation as a recurring issue.
Proof needs mapping and implementation evidence. This is exactly where KLEAP’s concierge model helps. By building a weekly workflow that keeps evidence current, assigns ownership, and drives remediation to closure, we ensure HIPAA readiness at all times.
How KLEAP Helps Healthcare Teams Stay Continuously Audit-Ready
Our approach reduces decision friction, tightens ownership, and keeps evidence current. That is what makes a HIPAA compliance audit predictable, even when teams are busy and systems keep changing. Here’s what we set up and what you get.
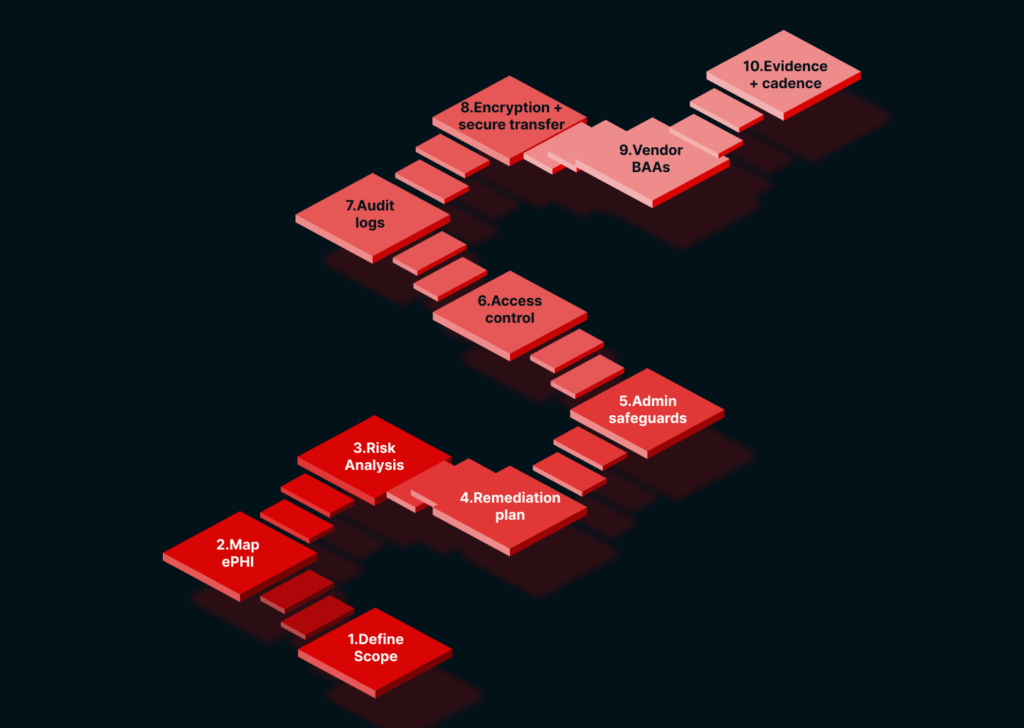
- Scope that auditors can follow
- Risk analysis that stays tied to action
- A remediation backlog with owners and acceptance criteria
- A system that records emerging evidence for continuous provenance
- Validation notes and incident readiness artifacts
KLEAP serves as your concierge for cybersecurity compliance. Whether it is in healthcare or manufacturing, we simplify security compliance readiness. Scope fast; translate requirements into a remediation checklist with owners, set up a weekly cadence, and package outcomes into an audit-ready process.