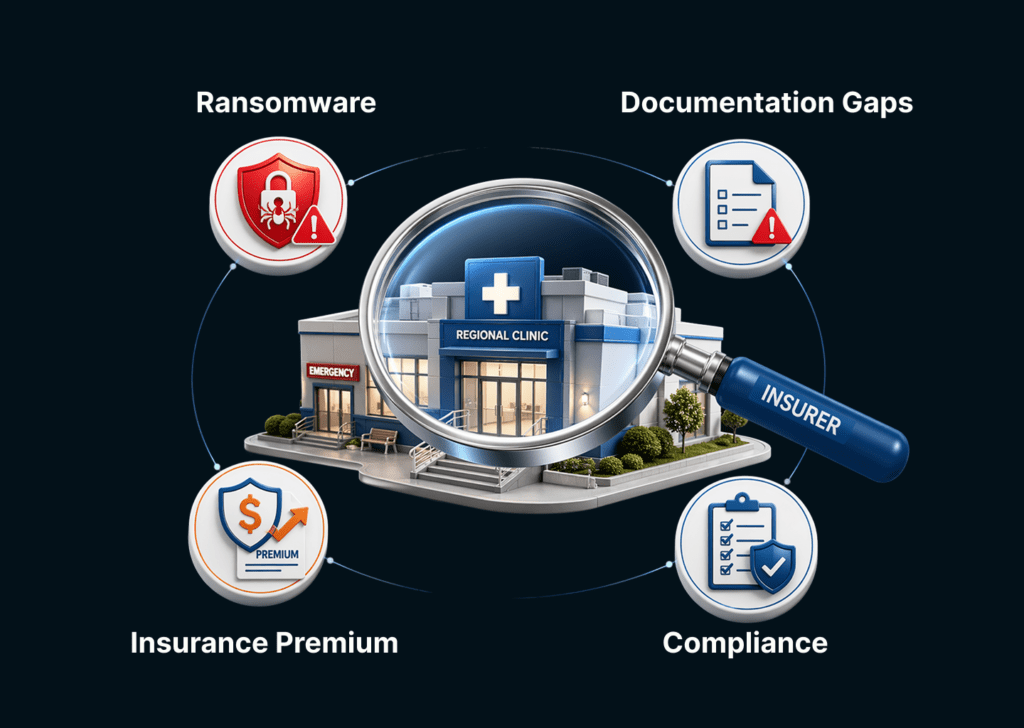
Cyber insurance renewals are getting tough. Underwriters are asking for supporting documentation and becoming stricter with their insurance pricing, which is rising day by day.
This presents a challenge for regional clinics who operate on tighter budgets and barebones IT teams. They are usually smaller outpatient providers serving local communities, often in rural or underserved areas.
The controls regional clinics have in place often aren’t always visible to the insurer. NIST CSF 2.0 certification changes that.
The NIST Cybersecurity Framework is a voluntary, risk-based set of guidelines developed by the National Institute of Standards and Technology to help organizations of any size manage cybersecurity risk.
It doesn’t prescribe tools but provides a structured, outcome-focused set of best practices that regulators, auditors, and insurers can recognize.
The introduction of NIST CSF 2.0 expanded the framework to a sixth function: Govern. It adds organizational policies, risk ownership, vendor oversight, and board-level accountability to the original five functions (Identify, Protect, Detect, Respond, Recover).
For regional clinics, the benefits of having NIST CSF 2.0 compliance are concrete.
A 2025 Healthcare Cybersecurity Benchmarking Study conducted across 54 healthcare providers by Censinet and other organizations found that healthcare organizations using the NIST CSF as their primary framework reported their premium increase was only one-third of the rate that organizations without the framework had to pay.
Still, regional clinics cannot be grouped together with other healthcare providers as they face a different kind of challenge.
The Reason Insurance Premiums Are Becoming a Big Concern for You
Regional clinics carry the same HIPAA exposure as large hospital systems without the security teams or budget to match. And that is becoming a problem.
Ransomware groups treat regional clinics as targets of opportunity: smaller security teams, legacy infrastructure, EHR integrations that weren’t designed with security in mind, and an operational pressure that makes paying a ransom feel faster than recovering from backup.
When a regional clinic gets hit by a ransomware attack, the consequences are immediate. The February 2026 ransomware attack on the University of Mississippi Medical Center forced seven hospitals and 35 clinics across the state to suspend operations. It is a direct illustration of how single incidents cascade across regional healthcare ecosystems.
IBM’s 2025 Cost of a Data Breach Report puts the average healthcare breach cost at $4.4 million last year. For a clinic operating on thin margins, that figure isn’t recoverable.
Cyber insurance is how most regional clinics manage that risk. But the market has responded to healthcare’s breach trajectory by tightening underwriting standards.
Projections show cyber insurance premiums will increase by 15 to 20 percent in 2026. Meanwhile, application questionnaires from underwriters have expanded from one page to fifteen. And the bar for what constitutes an acceptable security posture has risen substantially.
The specific problem for regional clinics is not that their security is necessarily worse than enterprise healthcare providers. It’s that they can’t demonstrate it in the language insurers understand.
Underwriters don’t have visibility into your network. They make decisions based on documentation, attestations, and third-party evidence. If those doesn’t exist, the underwriter prices accordingly, taking into consideration the worst case scenario.
What Cyber Insurance Underwriters Are Actually Looking For
Insurance carriers now use structured questionnaires that probe specific technical controls, not general security posture. The answers directly influence whether you qualify for coverage and at what premium.
The requirements fall into five essential security controls that underwriters evaluate across all sectors:
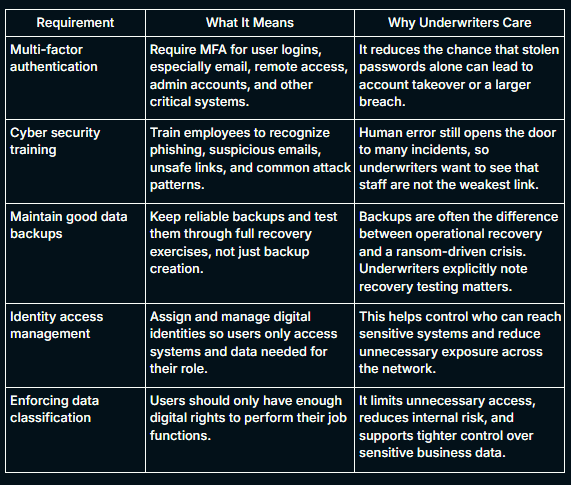
These days, underwriters have moved beyond checkbox attestations and now want proof that controls were enforced, logged, and working at the time of risk review or incident review. They look for a documented incident response plan with defined escalation procedures and tested playbooks.
Each of these questions corresponds to a specific underwriting risk factor. A clinic that can answer yes with supporting documentation is priced differently from those who cannot prove it.
What you may discover at the time of renewal is that you have controls in place that answer most of these questions affirmatively, but you may not have the documentation. NIST CSF 2.0 provides the structure to close that gap.
If you have older EHR-connected tools, billing applications or unsupported internal systems, and you cannot show evidence for patching, authentication, logging, and recovery readiness, the insurer only sees uncertainty.
In 2026, a carrier’s documentation baseline typically comprises:
- MFA Enforcement Evidence: Authentication logs that indicate active MFA to access email, financial systems, client data, and remote access to your network.
- Patch Event Logs: These are timestamped records of CVE remediations.
- EDR Deployment Reports: Carriers want proof that you’re actively monitoring for threats and updating security software among all end users.
- Incident Response Plan: Security awareness training and simulation-based planning is now not a recommendation, but a requirement.
- Software Inventory: This involves a detailed documentation of software components, versions, and patch statuses.
Penetration testing occupies a specific and non-negotiable position in this evidence stack. As it is, the January 2026 proposed update to the HIPAA Security Rule has introduced mandatory annual pentesting.
Carriers in 2026 will now require a manual penetration test report, which will also address both the Identify and Protect functions of the NIST CSF framework for healthcare.
How the Six Functions Map to Insurer Underwriting Criteria
NIST CSF 2.0’s six functions are designed to operate simultaneously to build a robust security posture across your organization. Each function corresponds directly to what cyber insurance underwriters probe during the renewal process.
1. Govern: Organizational Risk Ownership
The Govern function establishes that a clinic’s cybersecurity risk management strategy, expectations, and policies are defined, communicated, and actively monitored.
A clinic with a written security policy and a documented vendor risk review process is demonstrating the governance maturity that correlates with lower claim probability.
2. Identify: Know What You Are Protecting
The Identify function requires that an organization understands its current cybersecurity risks, specifically, its asset inventory, data flows, and the threat environment those assets operate in.
This means you need to map where ePHI lives across EHR systems, billing platforms, patient portals, email, and third-party integrations.
3. Protect: Safeguards in Place and Documented
The Protect function covers the safeguards a clinic uses to manage its cybersecurity risks: access controls, MFA, patch management, staff training, and data security.
This is also the most undocumented implementation in your clinic. If you have controls for MFA deployment and training, but they are not documented, they produce no underwriting value.
4. Detect: Finding and Analyzing Incidents
The Detect function covers the capabilities an organization uses to find and analyze possible cybersecurity attacks. Insurers weight this function heavily because detection speed directly correlates with breach size and cost.
A clinic with endpoint detection and response tools, centralized logging, and access review processes demonstrates Detect maturity.
5. Respond: Actions Taken After Detection
The Respond function requires that actions regarding a detected cybersecurity incident are defined and ready. Most cyber insurance applications ask directly whether an incident response plan exists and when it was last tested.
A clinic without a tested Incident Response Plan faces longer recovery timelines and higher breach costs that compound the insurance premium cost.
6. Recover: Restoring Operations After an Incident
The Recover function addresses how a clinic restores its assets and operations following a cybersecurity incident.
Even if you have daily backups, you should document the recovery test as it is what the carriers look for.
How You Can Align Your Clinic to NIST CSF 2.0: A Step-by-Step Guide
NIST CSF 2.0’s implementation guide identifies seven steps that move an organization from a lack of defined posture to a documented, actionable security program.
The sequence matters as each step builds on the last, and skipping ahead produces documentation that is inconsistent and difficult to defend at renewal.
Step 1: Prioritize and Scope
The first step is determining which parts of the clinic the NIST CSF framework will cover. For most regional clinics, the right starting scope is the systems and workflows that touch ePHI: the EHR platform, billing integrations, patient portal, clinical devices, and any third-party vendors with access to patient data.
Trying to apply the framework to every system simultaneously is not a realistic starting point for a clinic with a small IT team. You should define the boundary, document it, and use it consistently throughout the remaining steps.
Step 2: Orient the Organization
Before assessing controls, you need to understand the threat environment it is operating in, with HIPAA being a primary regulatory requirement if you’re touching PHIs.
This orientation step identifies the inputs that will shape the CSF profile: what risks matter most, what standards apply, and what the clinic already does that can be mapped to framework outcomes.
HIPAA requirements can be mapped directly to NIST CSF subcategories related to data security, access control, and audit logging, which means existing HIPAA work does not need to be redone, it needs to be documented and organized.
Step 3: Create a Current Profile
The Current Profile is a structured snapshot of the clinic’s cybersecurity posture as it exists today. Working through each of the six CSF functions (Govern, Identify, Protect, Detect, Respond, and Recover) the clinic documents which outcomes it currently meets, which it partially meets, and which are absent.
This step produces the baseline evidence that the rest of the program builds from. It is also the document that most directly answers an underwriter’s question about the organization’s current risk state.
Step 4: Conduct a Risk Assessment
With the Current Profile complete, the clinic conducts a risk assessment to identify the threats and vulnerabilities that are most relevant to its environment. For regional clinics, this includes ransomware targeting EHR and billing systems, phishing against clinical staff, insecure third-party vendor access, and unpatched web-facing applications.
The risk assessment does not need to be done every month. It should be focused, documented, and specific to the scoped environment identified in Step 1. The output is a prioritized list of risks that informs what the Target Profile needs to address.
Step 5: Create a Target Profile
The Target Profile describes the security posture you intends to reach, based on its risk assessment, regulatory obligations, and operational constraints.
The appropriate target tier should reflect your organization’s risk profile, not an idealized standard. Target Profiles aren’t static, so you need to revisit and revise them regularly to stay aligned with real-world conditions.
Step 6: Identify, Analyze, and Prioritize Gaps
The gap analysis compares the Current Profile against the Target Profile and produces a prioritized list of what needs to change. Prioritizing the gaps depends on two variables: the risk impact of the gap and the feasibility of closing it given the clinic’s resources.
For insurance purposes, the highest-priority gaps are those that correspond directly to underwriter questionnaire items: absent MFA documentation, no current pentest report, untested backups, and missing Incident Response Plan testing records.
These gaps are both high-impact from a security standpoint and high-consequence from a coverage standpoint, and you should address them first.
Step 7: Implement an Action Plan and Review Continuously
The final step is translating the gap analysis into a documented action plan with assigned owners, milestones, and target completion dates.
However, you should remember that the NIST CSF framework is not a one-time exercise. As you add service lines, new vendors, or new technology, the Current Profile should be updated to reflect those changes, and the gap analysis rerun.
For cyber insurance purposes, update your organizational profile and schedule a fresh penetration test before renewal, confirming that Incident Response Report tabletop exercises and backup recovery tests are documented and current.
A clinic that treats CSF alignment as an ongoing program, rather than a one-time audit preparation exercise, is the clinic that arrives at each renewal with a stronger underwriting profile than it had the year before.
How KLEAP can help
Aligning to NIST CSF 2.0 before an insurance renewal is a sequential process. You have to scope, profile, perform gap analysis, penetration testing, and evidence packaging.
Most regional clinic IT teams don’t have the bandwidth to run it alongside daily operations.
KLEAP’s concierge model is built for exactly this. Every engagement is led by a single dedicated security expert who stays with your clinic from the initial gap assessment through to the completed evidence package.
One person who understands your EHR integrations, your vendor relationships, and your renewal timeline.
In practice, that means we map your current posture against all six NIST CSF 2.0 functions, identify which controls are documented and which aren’t, and conduct a manual penetration test scoped to your actual environment.
This includes web applications, APIs, network infrastructure, and EHR integrations among others. We then produce a report that maps directly to HIPAA Security Rule requirements and NIST CSF 2.0 categories.
The same report serves as your remediation roadmap, your HIPAA audit evidence, and your underwriting artifact.
If your renewal is approaching and you don’t yet have a current pentest report, a tested incident response plan, or a documented vendor risk inventory, those are the gaps that cost the most at the underwriting table.
We at KLEAP help you close them in the right order, with the right documentation, before the questionnaire arrives.